justCTF 2019
Contents
Reverse
FSMir
We managed to intercept description of some kind of a security module, but our intern does not know this language. Hopefully you know how to approach this problem.
We get a file fsmir.sv.
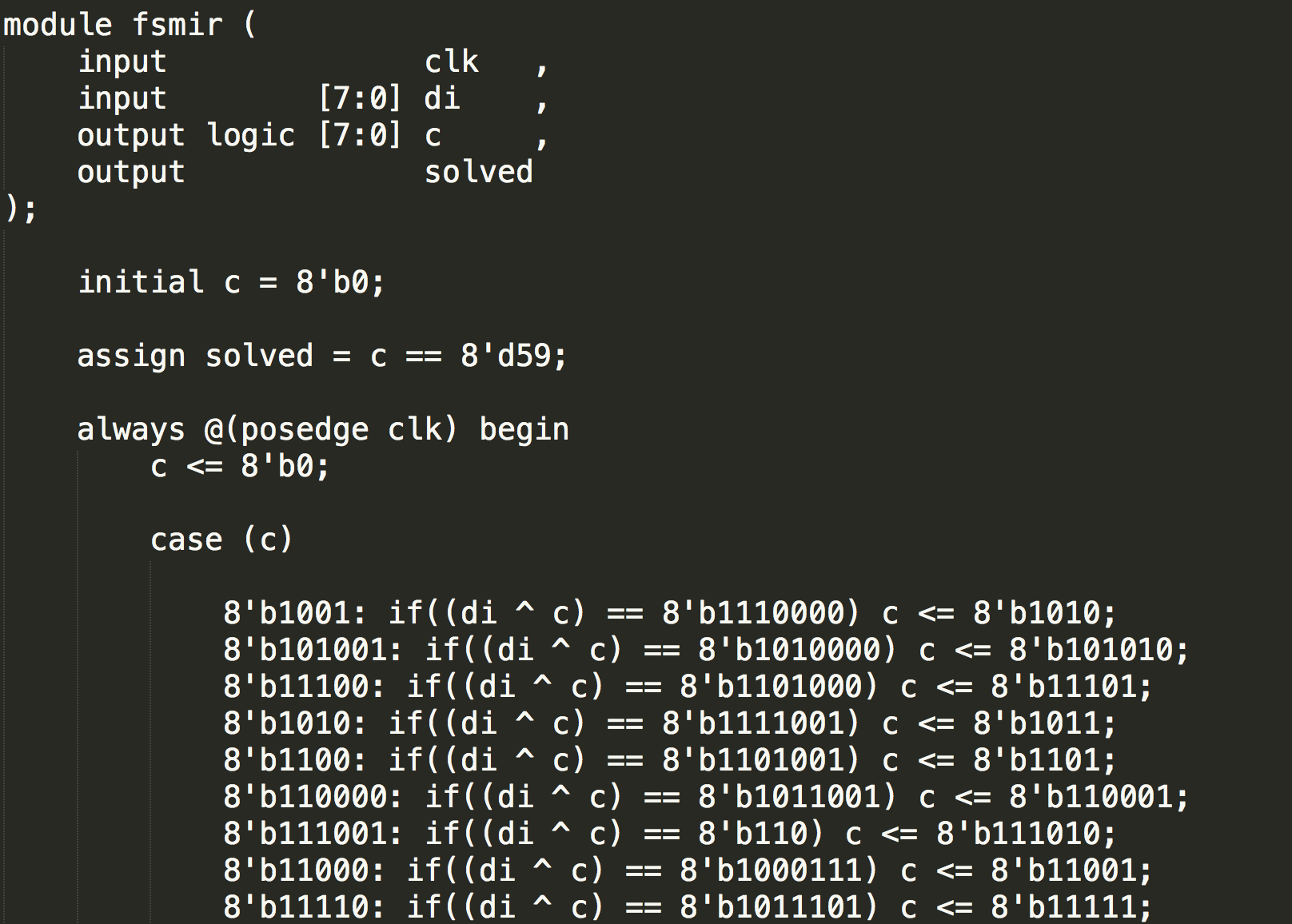
In the file, we get these contents. It is written in SystemVerilog. It starts at c = 8'b0, and ends when c = 8'd59. We notice that everytime a case is done, c will increase 1. di should be our flag.
I write a script in python to collect di.
|
|
And we can get the flag justCTF{SystemVerilog_is_just_C_with_fancy_notation_right?}.
FSMir2
We intercepted yet another security module, this time our intern fainted from just looking at the source code, but it’s a piece of cake for a hacker like yourself, right?
We get a file fsmir2.sv.
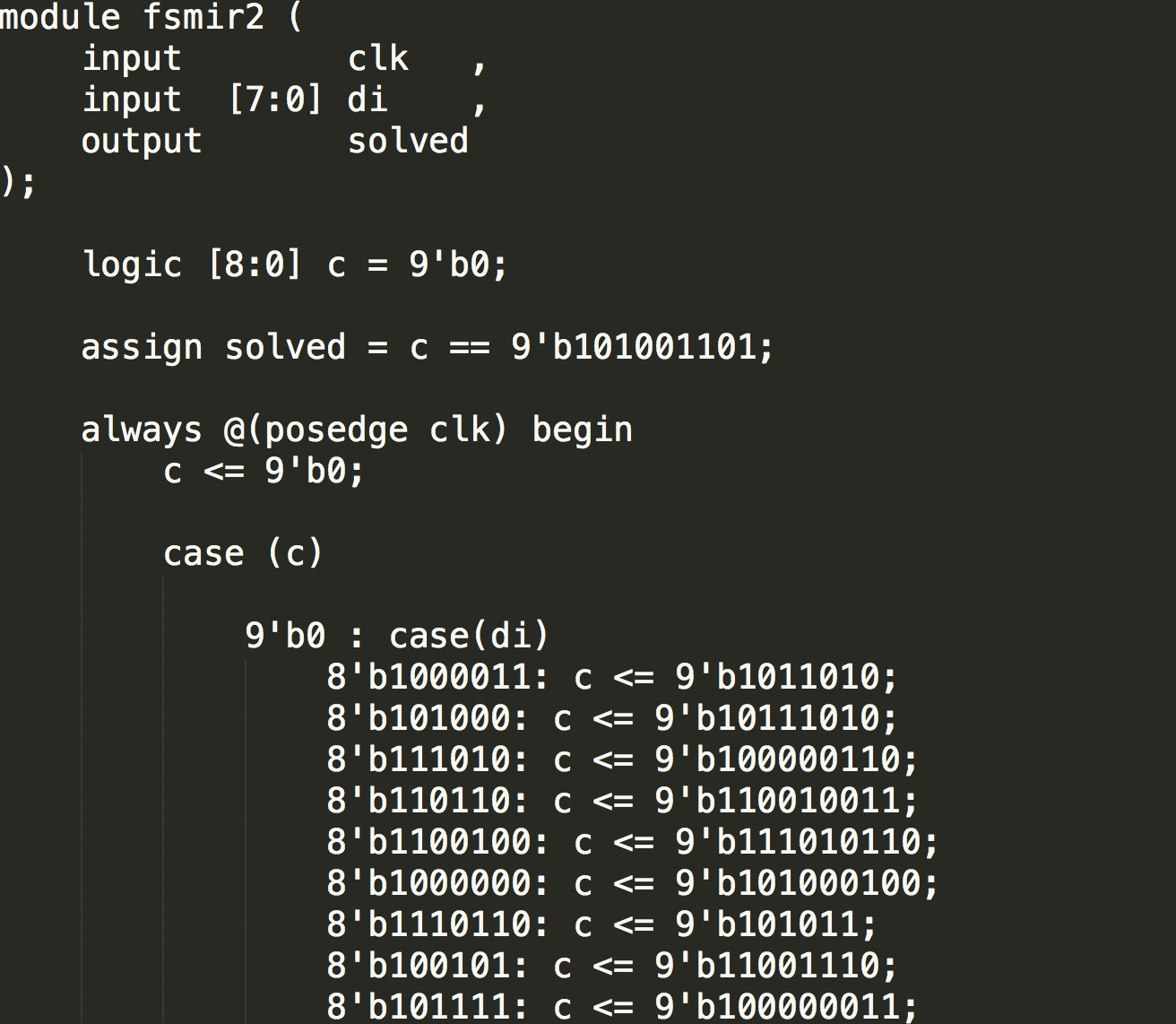
In the file, we get these contents. It is written in SystemVerilog. It starts at c = 9'b0, and ends when c = 9'b101001101. There are two cases, the first one takes c as input, and the second one takes di as input.
Character j is 0b1101010 in binary. When c is 9'b0, there is a line 8'b1101010: c <= 9'b111110010;, and c = 9'b111110010 is the next case after c = 9'b0. We need to find the right di so that c can equals to the next case. When c = 9'b101001101, it finishes.
I write a script in python to collect di
|
|
And we can get the flag justCTF{I_h0p3_y0u_us3d_v3r1L4t0r_0r_sth...}.
MISC, PPC
Dominoes
I found a very old set of dominoes: puzzles.txt
The hidden inscription scrapped on the box says:
The truth split into the pieces is the key.
But remember, there is only one true truth!
I suspect the key to be a semantically correct and meaningful sentence consisted of lowercase english words only. Can you help me uncover the key?
The flag is the recovered sentence wrapped into justCTF{} format.
We get a file puzzles.txt.
|
|
I solve it by hand. E.g. there is zzl. I thought it is the word puzzle, and I find segments _pu, puz, uzz, zzl, zle in the file to create puzzle. There is olv, and I find segments l_s, _so, sol, olv, lve, ve_ to create solve.
At last, we can get the string there_was_no_single_doubt_in_my_mind_that_great_player_like_you _shall_solve_the_puzzle.
Author L3o
LastMod 2019-12-23